一、什么是数据安全风险评估
对数据和数据处理活动安全进行信息调研、风险识别、风险分析和风险评价的整个过程。数据安全风险评估,主要围绕数据和数据处理活动,聚焦可能影响数据的保密性、完整性、可用性和数据处理合理性的安全风险,掌握数据安全总体状况,发现数据安全隐患,提出数据安全管理和技术 防护措施建议,提升数据安全防攻击、防破坏、防窃取、防泄露、防滥用能力。首先通过信息调研识别数据处理者、业务和信息系统、数据资产、数据处理活动、安全措施等相关要素,然后从数据安全管理、 数据处理活动、数据安全技术、个人信息保护等方面识别风险隐患,最后梳理风险源清单,分析数据安全风险、视情评价风险,并给出整改建议。
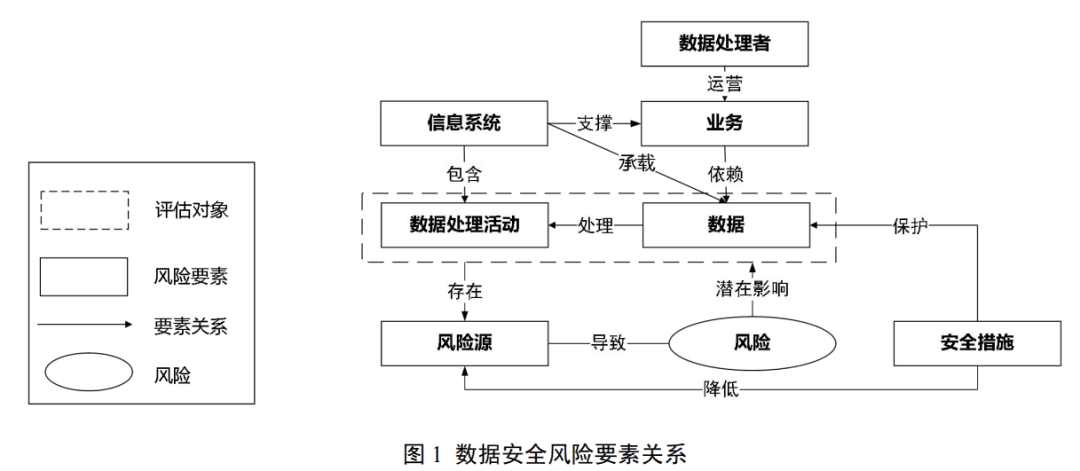
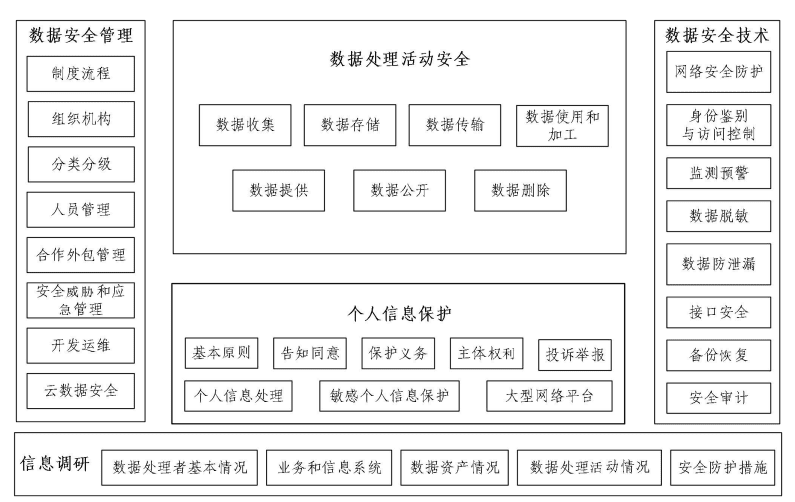
二、数据安全风险要素关系
数据安全风险评估涉及数据、数据处理活动、业务、信息系统、安全措施、风险源等基本要素,要素间关系如图1所示。数据和数据处理活动是数据安全风险评估的评估对象。
三、数据安全风险评估的主要内容信息调研:
对可能影响数据安全风险的要素的情况调研,包括数据处理者、业务和信息系统、数据资产、数据处理活动、数据安全防护措施。掌握数据处理者、业务和信息系统基本情况,梳理涉及的数据资产和数据处理活动,了解采取的数据安全防护措施情况,掌握被评估对象或同行业相关数据安全事件历史发生情况。
(一)风险识别:
基于信息调研情况,从数据安全管理、数据处理活动安全、数据安全技术、个人信息保护等方面进行数据安全风险识别,识别评估对象现有安全措施完备性并对其有效性进行验证,识别可能存在的风险源。
(二)风险分析与评价:
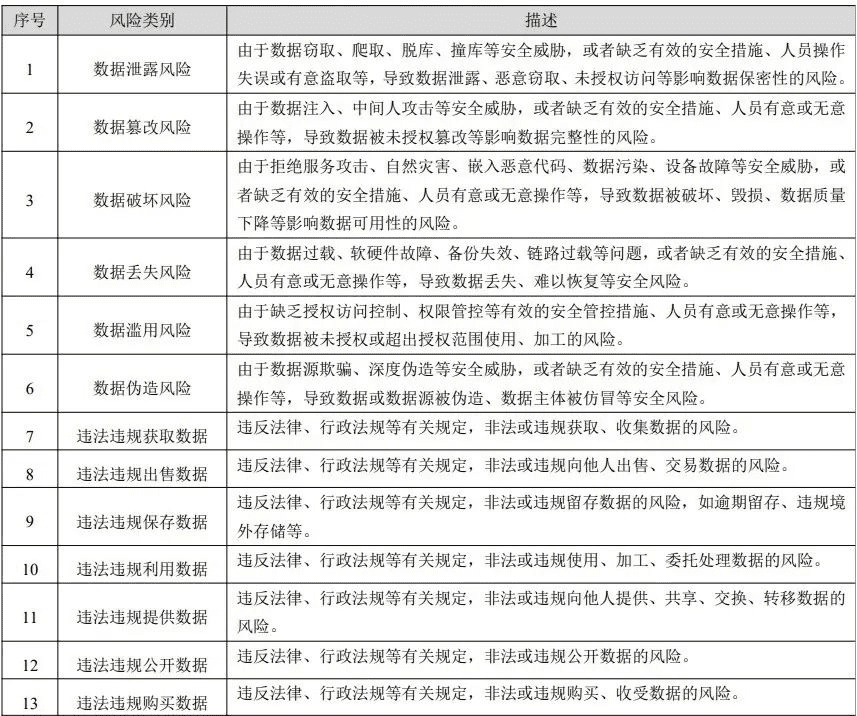
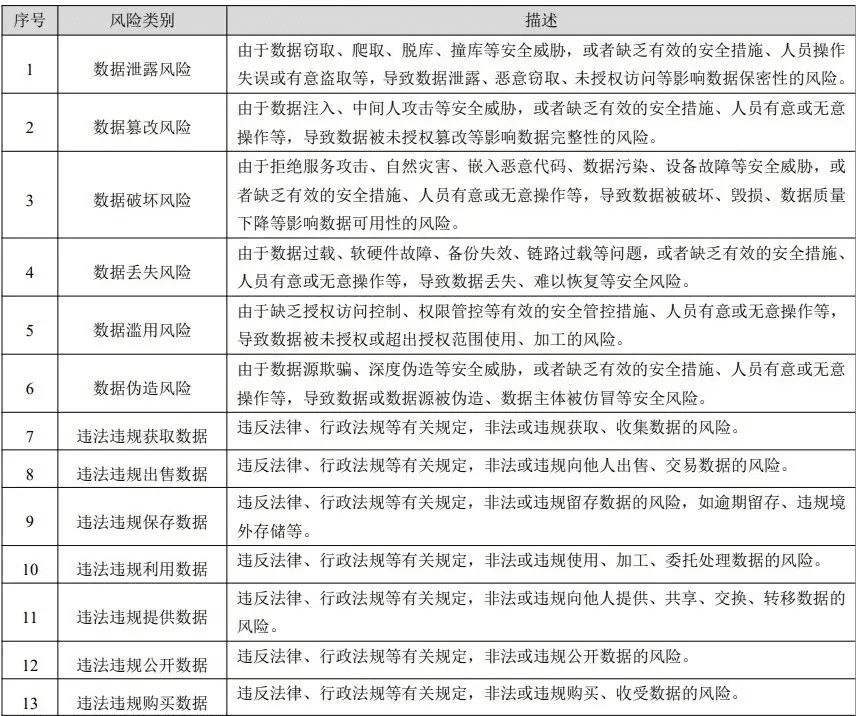
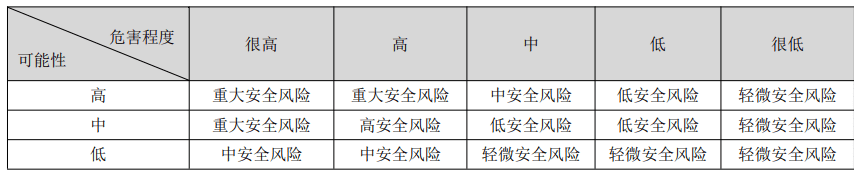
通过分析风险类型、风险危害程度和可能性,评价风险等级。
1) 数据安全风险分析,包括数据安全风险归类、风险危害程度分析、风险 发生可能性分析。
2) 风险归类分析,结合风险源可能引发的风险类型,对风险源进行归类。
3) 风险危害程度分析,从数据价值、数据重要性、风险源危害程度等方面,综合评价风险可能对国家安全、公共利益或者个人、组织合法权益造成的危害程度。
4) 风险发生可能性,从风险源发生频率、安全措施有效性和完备性、风险源关联性等方面, 综合评价风险发生的可能性。
5) 风险评价过程,一般根据风险危害程度和风险发生可能性评价数据安全风险,得到数据安 全风险级别,梳理形成数据安全风险清单。
四、六种适用情形
情形一:重要数据处理者、关键信息基础设施运营者、处理 100 万人以上个人信息的个人信息处理者、大型互联网平台运营者、赴境外上市的数据处理者、党政机关、网络安全等级保护三级及以上运营者,应每年开展一次数据安全风险评估。
情形二:数据处理者在重要数据共享、交易、委托处理或向境外提供前,应开展数据安全风险评估。
情形三:数据处理者开展高风险数据处理活动前,宜开展数据安全风险评估,高风险数据处理活动包括 但不限于: 数字化转型网www.szhzxw.cn
1) 重要数据和个人信息处理者合并、分立、解散、被宣告破产进行数据转移。
2) 承载重要数据处理活动的信息系统发生架构调整、下线等重大变更。
3) 数据处理者利用生物特征进行个人身份认证。
4) 基于不同业务目的的数据汇聚融合。
5) 委托处理、向他人提供未成年人、老年人数据。
6) 新技术应用可能带来数据安全风险的。
7) 法律法规或有关部门规定要评估的情形。 数字化转型网www.szhzxw.cn
8) 其他可能直接危害国家安全、公共利益或者大量个人、组织合法权益的数据处理活动。
情形四:对于已经评估过数据安全风险评估的数据处理活动,当数据范围、数据处理活动、环境、相关方等发生重大变更时,需重新开展数据安全风险评估。
情形五:重要系统上线前,可根据实际需要开展数据安全风险评估。
情形六:当被评估对象的政策环境、外部威胁环境、业务目标、安全目标等发生重大变化时,应重新开 展风险评估。
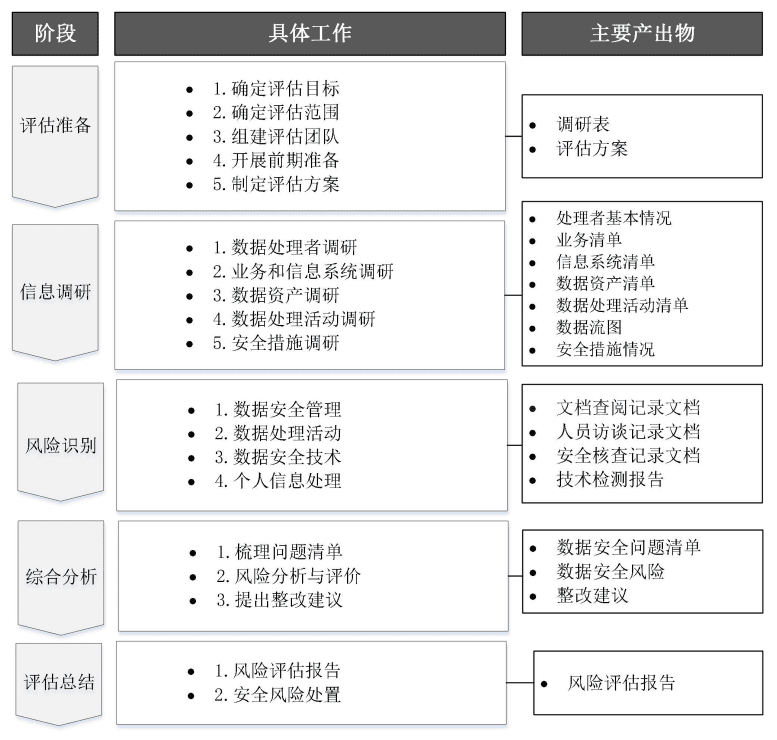
五、数据安全风险评估实施流程第一阶段——评估准备:
是数据安全风险评估的初始预备阶段,在评估实施前应完成评估准备工作。形成调研表、数据安全风险评估方案等。
(一)确定评估目标:
a)摸清数据种类、规模、分布等基本情况;
b)摸清数据处理活动的情况;
c)发现可能影响国家安全、公共利益或者个人、组织合法权益的数据安全问题和风险
d)发现共享、交易、委托处理、向境外提供重要数据等处理活动的数据安全问题和风险; 数字化转型网www.szhzxw.cn
e)促进完善数据安全保护措施,提升数据安全保护能力。
(二)确定评估范围:
根据工作需要和评估目标,确定数据安全风险评估的对象、范围和边界,明确评估涉及的数据资产、 数据处理活动、业务和信息系统、人员和内外部组织等。数据安全风险评估聚焦数据和数据处理活动,评估范围可以是某个单独的业务、信息系统、部门涉及的数据和数据处理活动,可以是组织全部数据和 数据处理活动。
(三)组建评估团队:
数据处理者自行或委托第三方专业技术机构开展数据安全风险评估时,可组织业务、安全、法务、合规、运维、研发等相关部门参与实施,评估组长由数据安全负责人或授权代表担任,也可委托第三方专业技术机构实施。第三方机构在评估中获取的信息只能用于评估目的,未经授权不应泄露、出售或者非法向他人提供。 数字化转型网www.szhzxw.cn
(四)开展前期准备:
开展数据安全风险评估前期准备时,应根据评估目标、评估范围和调研情况,制定工作计划、确定评估依据、确定评估内容、建立评估文档。
(五)制定评估方案:
评估团队编制数据安全风险评估工作方案并获得评估管理方的支持、认可,方案内容包括但不限于:评估概述、评估内容和方法、评估人员、实施计划、工作要求、测试方案。
第二阶段——信息调研:
主要用于识别数据处理者的基本情况,厘清其与业务和信息系统的关系,处理的数据和开展的数据处理活动情况,采取的数据安全防护措施。形成数据处理者基本情况、业务清 单、信息系统清单、数据资产清单、数据处理活动清单、安全措施情况等,具备条件的,可绘制数据流图。 数字化转型网www.szhzxw.cn
(一)数据处理者调研:
数据处理者的基本情况,包括单位基本情况、单位性质、是否属于特定类型数据处理者、所属行业、业务运营地区、主要业务范围等。
(二)业务和信息系统调研:
包括网络和信息系统基本情况、业务基本信息、业务涉及个人信息及重要数据数据处理情况等。
(三)数据资产调研:
梳理结构化数据资产(如数据库表等)和非结构化数据资产(如图表文件等),摸清数据底数,输 出数据资产清单。涉及范围包括但不限于生产环境、测试环境、备份存储环境、云存储环境、个人工作 终端、数据采集设备终端等收集和产生的数据。
(四)数据处理活动调研:
针对评估对象和范围,梳理数据处理活动清单,验证或绘制数据流图。数据流图应描述数据流转各 环节经过的相关方、信息系统,以及每个流动环节涉及的数据类型等。
(五)安全防护措施识别:
调研已有安全措施情况,包括已开展的等级保护测评、商用密码应用安全性评估、安全检测、风险评估、安全认证、合规审计情况,及发现问题的整改情况、数据安全管理组织、人员及制度情况等。
第三阶段——风险识别:
针对各个评估对象,从数据安全管理、数据处理活动、数据安全技术、个人信息保护等方面,通过多种评估手段识别可能存在的数据安全风险隐患。形成文档查阅记录文档、人员访谈记录文档、安全核查记录文档、技术检测报告等。 数字化转型网www.szhzxw.cn
数据安全管理:应从数据安全管理制度、安全组织机构、分类分级管理、合作外包管理、安全威胁和应急管理、开发运维管理、云数据安全等方面识别数据安全管理风险。
数据处理活动安全:数据收集安全风险识别、数据存储安全风险识别、 数据传输安全风险识别、数据使用和加工安全风险识别、数据提供安全风险识别、数据公开安全风险识别、数据删除安全风险识别、其他数据处理活动安全风险识别。
数据安全技术:应从网络安全防护、身份鉴别与访问控制、检测预警、数据脱敏、数据防泄漏、数据接口安全、数 据备份与恢复、安全审计等方面识别数据安全技术风险。
个人信息保护:如被评估范围涉及个人信息处理,还应从个人信息处理基本原则、个人信息告知同意、个人信息处理、敏感个人信息处理、个人信息主体权利、个人信息安全义务、个人信息投诉举报、大型网络平台个人信息保护等方面识别个人信息保护风险。 数字化转型网www.szhzxw.cn
第四阶段——风险分析与评价:
在风险识别基础上开展风险分析,并视情对风险进行评价,最后提出整改建议。形成数据安全风险源清单、数据安全风险列表、整改建议等。
第五阶段——评估总结:编制数据安全风险评估报告,开展风险处置。
六、数据安全风险评估内容框架
数据安全风险评估,在信息调研基础上,围绕数据安全管理、数据处理活动安全、数据安全技术、 个人信息保护等方面开展评估。
七、数据安全风险评估手段人员访谈:
对相关人员进行访谈,核查制度规章、防护措施、安全责任落实情况。 数字化转型网www.szhzxw.cn
文档查验:查验安全管理制度、风险评估报告、等保测评报告等有关材料及制度落实情况的证 明材料。
安全核查:核查网络环境、数据库和大数据平台等相关系统和设备安全策略、配置、防护措施 情况。
技术测试:应用技术工具、渗透测试等手段查看数据资产情况、检测防护措施有效性。

英文翻译:
What is data security risk assessment
The whole process of information research, risk identification, risk analysis and risk assessment for the security of data and data processing activities. Data security risk assessment mainly focuses on data and data processing activities, focusing on security risks that may affect the confidentiality, integrity, availability and rationality of data processing, master the overall situation of data security, discover data security risks, and put forward suggestions on data security management and technical protection measures. 数字化转型网www.szhzxw.cn
Improve data security against attack, destruction, theft, disclosure, and abuse. Firstly, data processors, business and information systems, data assets, data processing activities, security measures and other relevant elements are identified through information research, and then hidden risks are identified from data security management, data processing activities, data security technology, personal information protection and other aspects. Finally, the list of risk sources is sorted out, data security risks are analyzed, and risks are evaluated according to the situation. And give corrective suggestions.
Relationship between data security risk factors
Data security risk assessment involves data, data processing activities, business, information systems, security measures, risk sources and other basic elements. And the relationships among these elements are shown in Figure 1. Data and data processing activities are the subject of data security risk assessment.
Third, the main content of data security risk assessment information research:
A survey of factors that may affect data security risks, including data processors, business and information systems, data assets, data processing activities. And data security safeguards. Master the basic situation of data processors, businesses and information systems, sort out the data assets. And data processing activities involved, understand the data security protection measures taken. And master the history of data security incidents related to the evaluated object or the same industry.
Risk identification: Based on information research, data security risks are identified from the aspects of data security management, data processing activity security, data security technology, personal information protection, etc., the completeness of existing security measures of the assessed objects is identified and their effectiveness is verified, and possible risk sources are identified.
Risk analysis and evaluation:
The risk level is evaluated by analyzing the risk type, risk hazard degree and possibility.
1) Data security risk analysis, including data security risk classification, risk harm degree analysis, risk probability analysis.
2) Risk classification analysis, risk sources are classified according to the types of risks that may be caused by risk sources.
3) Risk and harm degree analysis, from the aspects of data value, data importance, risk source harm degree, etc., to comprehensively evaluate the degree of harm that risks may cause to national security, public interests or legitimate rights and interests of individuals and organizations.
4) Risk occurrence possibility: Comprehensively evaluate risk occurrence possibility from the aspects of risk source occurrence frequency, effectiveness. And completeness of safety measures, risk source correlation, etc.
5) In the risk assessment process, data security risks are generally evaluated according to the degree of risk harm and the possibility of risk occurrence, data security risk levels are obtained . And a list of data security risks is sorted out.
Four, six applicable situations
Situation 1: Important data processors, critical information infrastructure operators, personal information processors processing more than 1 million people’s personal information, large Internet platform operators, data processors listed overseas, party and government agencies, network security level protection level 3 and above operators, should carry out a data security risk assessment every year.
Situation 2: Data processors should carry out data security risk assessment before sharing, trading, processing or providing important data overseas.
Situation 3: Data processors should carry out data security risk assessment before carrying out high-risk data processing activities, including but not limited to:
1) Merger, division, dissolution, and bankruptcy of important data and personal information processors for data transfer. 数字化转型网www.szhzxw.cn
2) The information system carrying important data processing activities has undergone major changes such as structural adjustment and offline.
3) Data processors use biometrics for personal identity authentication.
4) Data convergence and fusion based on different business purposes.
5) Entrust processing and provide data of minors and elderly people to others.
6) The application of new technologies may bring data security risks.
7) Situations to be assessed as required by laws and regulations or relevant departments.
8) Other data processing activities that may directly endanger national security, public interests or the legitimate rights and interests of a large number of individuals and organizations.
Scenario 4: For the data processing activities that have been evaluated for data security risk assessment, the data security risk assessment shall be re-conducted when there are significant changes in the data scope, data processing activities, environment, relevant parties, etc. 数字化转型网www.szhzxw.cn
Situation 5: Before important systems go online, data security risk assessment can be carried out according to actual needs.
Situation 6: When the policy environment, external threat environment, business objectives, security objectives, etc .Of the assessed object have changed significantly, the risk assessment should be re-opened.
Data security risk assessment implementation process
The first stage – Assessment preparation:
is the initial preparatory stage of the data security risk assessment, and the assessment preparation should be completed before the assessment is implemented. Develop research tables, data security risk assessment plans, etc.
(1) Determine the evaluation objectives:
a) Find out the basic information such as the type, scale and distribution of data;
b) Mapping out data processing activities;
c) Identify data security issues and risks that may affect national security, public interests or the legitimate rights. And interests of individuals and organizations
d) Discover data security problems and risks in processing activities such as sharing, trading, entrusted processing. And providing important data overseas;
e) Promote the improvement of data security protection measures and enhance data security protection capabilities.
(2) Determine the scope of assessment:
According to the work needs and assessment objectives, determine the object, scope and boundary of data security risk assessment. And specify the data assets, data processing activities, business and information systems, personnel. And internal and external organizations involved in the assessment. Data security risk assessment focuses on data and data processing activities. The scope of the assessment can be the data and data processing activities involved in a single business, information system, department, or the entire data and data processing activities of the organization.
(3) Setting up an evaluation team:
When data processors themselves or entrust third-party professional and technical institutions to carry out data security risk assessment, they can organize relevant departments such as business, security, legal affairs, compliance, operation and maintenance, and research and development to participate in the implementation, and the assessment team leader is the data security person in charge or authorized representative, or they can entrust third-party professional and technical institutions to carry out the assessment. The information obtained by the third party during the evaluation shall only be used for the purpose of the evaluation and shall not be disclosed, sold or illegally provided to others without authorization. 数字化转型网www.szhzxw.cn
(4) Carry out preliminary preparations:
In the preliminary preparation for data security risk assessment, work plans, assessment basis, assessment content and assessment documents should be established according to the assessment objectives, assessment scope and investigation.
(5) Formulate evaluation plans:
The assessment team shall prepare the data security risk assessment work plan and obtain the support and approval of the assessment manager. The plan includes but is not limited to: assessment overview, assessment content and methods, assessment personnel, implementation plan, work requirements, and test plan.
The second stage – Information research:
It is mainly used to identify the basic situation of the data processor, clarify its relationship with the business and information system, the data processed and the data processing activities carried out, and the data security protection measures taken. Form the basic information of the data processor, business clearance, information system list, data asset list, data processing activity list, security measures, etc. If conditions are met, the data flow diagram can be drawn. 数字化转型网www.szhzxw.cn
(1) Survey of data processors:
The basic information of the data processor, including the basic information of the unit, the nature of the unit, whether it belongs to a specific type of data processor, its industry, its business operation region, and its main business scope.
(2) Business and information system research:
It includes the basic information of network and information system, basic business information, personal information involved in business and important data processing.
(3) Data asset research:
Organize structured data assets (such as database tables, etc.) and unstructured data assets (such as chart files, etc.), find out the data base, and input the list of data assets. Data collected and generated in production environments, test environments, backup storage environments, cloud storage environments, personal work terminals, and data collection device terminals are involved.
(4) Research on data processing activities:
Comb through the list of data processing activities and validate or map the data flow for the assessed object and scope. The data flow diagram should describe the relevant parties and information systems through which each link of the data flow passes, and the types of data involved in each flow link.
(5) Identification of safety protection measures:
Investigate existing security measures, including grade protection assessment, commercial password application security assessment, security testing, risk assessment, security certification, compliance audit, rectification of problems found, data security management organization, personnel and system, etc.
Stage 3 – Risk Identification:
For each assessment object, from data security management, data processing activities, data security technology, personal information protection and other aspects, through a variety of assessment methods to identify potential data security risks. Form document reference record document, personnel interview record document, safety verification record document, technical testing report, etc.
Data security management: Data security management risks should be identified from aspects such as data security management system, security organization, classification and classification management, cooperative outsourcing management, security threat and emergency management, development operation and maintenance management, and cloud data security.
Data processing activities security: data collection security risk identification, data storage security risk identification, data transmission security risk identification, data use and processing security risk identification, data provision security risk identification, data disclosure security risk identification, data deletion security risk identification, other data processing activities security risk identification.
Data security technology: Data security technology risks should be identified from the aspects of network security protection, identity authentication and access control, detection and early warning, data desensitization, data leakage prevention, data interface security, data backup and recovery, and security audit. 数字化转型网www.szhzxw.cn
Personal information protection: If the scope of the assessment involves the processing of personal information, the risks of personal information protection should also be identified from the basic principles of personal information processing, personal information consent, personal information processing, sensitive personal information processing, the rights of personal information subjects, personal information security obligations, personal information complaints and reports, and personal information protection on large network platforms.
The fourth stage — risk analysis and evaluation:
carry out risk analysis on the basis of risk identification, and evaluate the risk according to the situation, and finally put forward rectification suggestions. Form a list of data security risk sources, a list of data security risks, and rectification suggestions.
The fifth stage – assessment summary:
compile data security risk assessment report and carry out risk disposal.
Data security risk assessment content framework
Data security risk assessment, based on information research, focuses on data security management, data processing activities security, data security technology, personal information protection and other aspects of the assessment.
Data security risk assessment method personnel Interview:
Conduct interviews with relevant personnel to verify the implementation of rules and regulations, protective measures and safety responsibilities.
Document inspection: check the safety management system, risk assessment reports, and other relevant materials and system implementation evidence materials.
Security verification: verification of network environment, database and big data platform and other related systems and equipment security policies, configuration, protection measures.
Technical testing: Use technical tools, penetration testing and other means to view data assets and test the effectiveness of protective measures.
本文由数字化转型网(www.szhzxw.cn)转载而成,来源于 数字化转型战略指南;编辑/翻译:数字化转型网小汤圆。

免责声明: 本网站(http://www.szhzxw.cn/)内容主要来自原创、合作媒体供稿和第三方投稿,凡在本网站出现的信息,均仅供参考。本网站将尽力确保所提供信息的准确性及可靠性,但不保证有关资料的准确性及可靠性,读者在使用前请进一步核实,并对任何自主决定的行为负责。本网站对有关资料所引致的错误、不确或遗漏,概不负任何法律责任。
本网站刊载的所有内容(包括但不仅限文字、图片、LOGO、音频、视频、软件、程序等) 版权归原作者所有。任何单位或个人认为本网站中的内容可能涉嫌侵犯其知识产权或存在不实内容时,请及时通知本站,予以删除。