本文由CIAPH根据原西安杨森信息技术总监蒙伟在“CIAPH第三届生物药企数字创新峰会暨走进晶泰科技”活动上的分享整理。
随着数字化时代的推进,数据信息为各行各业注入了强大的动力,为各领域提供了有力的支持。然而,随之而来的是日益增加的数据安全风险。医药行业与其他领域的信息基础设施不尽相同,因为它直接关系到人们的生命安全。该领域的数据具有特殊性质,使其成为攻击者关注的焦点。
在“CIAPH第三届生物药企数字创新峰会暨走进晶泰科技”活动上,原西安杨森信息技术总监蒙伟从其亲身经验出发,分享了如何应对医药行业信息安全新趋势,同时还带来了实际的案例,下文为详细内容。

各位业界同仁,大家好,我是蒙伟。随着互联网、云计算以及人工智能的不断发展,数字化转型为企业带来了全新的安全挑战。在医药行业中,信息安全问题的重要性愈发凸显。因此,今天我将以信息安全为主题,分享我近年来在这方面的实践和经验,与大家共同探讨。
过去我们在谈论信息安全时主要关注如何有效管理网络、确保数据传输安全以及加强加密措施。然而,随着技术的不断发展,信息安全已经演变成更广泛的概念,包括合规管理、与业务的融合,甚至涉及人工智能的治理和规范,以及企业内部行为的规范化。当前,企业频繁受到勒索者病毒的威胁,因此如何预防这类威胁需要从意识形态、技术、流程等多个方面共同着手,以杜绝安全隐患事件的发生。
通常在企业制定安全策略和抵御风险方面,了解企业自身的优劣势和行业的经验至关重要,建议定期可以和业内的同行进行交流,并与合作伙伴保持沟通。以便于正确评估合理的信息安全解决方案。尤其在《网络安全法》和《个人信息保护法》发布后,需要第一时间对企业所有数据进行全面梳理,了解数据的存放位置和作用,这对于后续的跟进措施至关重要。只有对数据有足够了解,才能够迅速处理隐私和敏感数据,同时改进和整理的工作也会更加顺利。除此之外企业应该通过技术手段对数据进行分级保护和加密。在员工使用数据时,确保企业有明确的流程和规章制度,以防止不当访问造成泄漏。因此,需要采用有效的方法来防止数据流失和泄漏。最后,通过一系列治理原则,全方位管控数据,从技术手段到终端控制,实现全流程的数据安全防护。 数字化转型网(www.szhzxw.cn)

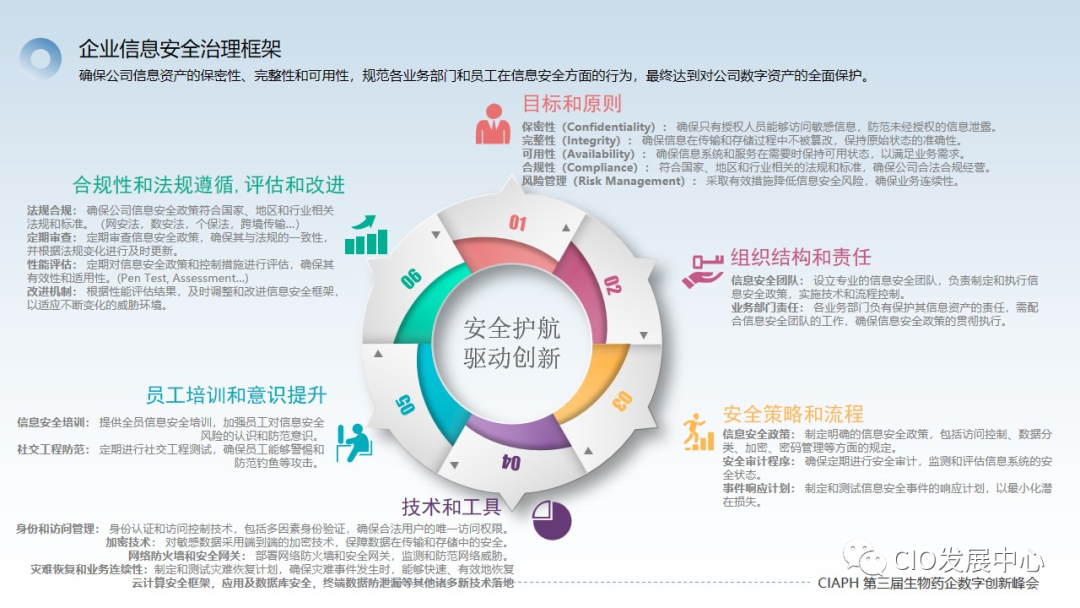
企业信息化发展到一定阶段,必然需要建立完整的数据安全治理框架。以下是这一过程的简要介绍:
- 首先,确定适应企业发展阶段的目标。这些目标可以涵盖安全性、完整性、可用性、合规性和风险管理等方面。
- 人员参与:为实现设定的目标,需要有相应的人员参与,甚至可以组建专门的团队来负责。对于小型IT团队,兼职参与也是可行的;对于大型IT团队,最好设立专门的安全岗位。
- 制定安全策略和流程:建立一套安全策略和流程,以使整个企业清晰了解如何保护数据。
- 选择技术和工具:找到适用的技术和工具,如备份、防泄漏和加密技术。确保有专门的同事负责,以避免不同数据库采用不同技术而导致混乱。一旦策略和技术统一,管理变得更为便捷。
- 员工培训:在安全领域,安全不仅是IT部门的事,而应该是整个企业的责任。因此,员工培训至关重要,需涵盖一线人员和管理层。 数字化转型网(www.szhzxw.cn)
- 遵守法律法规:面对不断新增的法律法规,确保企业合规是必要的。违反法规不仅影响公司声誉,还可能导致罚款,对企业财务报表产生不良影响。
今天的分享中,我为大家带来了两个案例。
首先,我们分享网安法与计算机等级保护相关的内容。随着数字化的不断深入,我们发现不仅在IT领域,企业的业务部门、研发部门等除了IT以外的部门也日益重视安全问题。从案例中项目架构我们可以看到,推进国家的计算机等级保护项目需要众多团队的协作,同时也需要将总部的一些关键职能部门纳入考虑范围,因为他们可能对数据、架构、技术以及现有的营销和研发方案产生影响。总体而言,获得国家级的等级保护认证是一个过程,而且并非一劳永逸。例如,如果是二级等保,需要每两年进行一次申报,而三级等保则需要每年进行一次。当然,这些工作都需要有相应的费用支撑,因此在项目初期,我们必须慎重考虑是否有足够的预算来支持这一过程,数据安全不应当只是一句空话,真正能够落地是需要得到老板和公司管理层的支持,因为每一步的行动都需要资金来提供保障,没有预算的支持一切都是空谈。
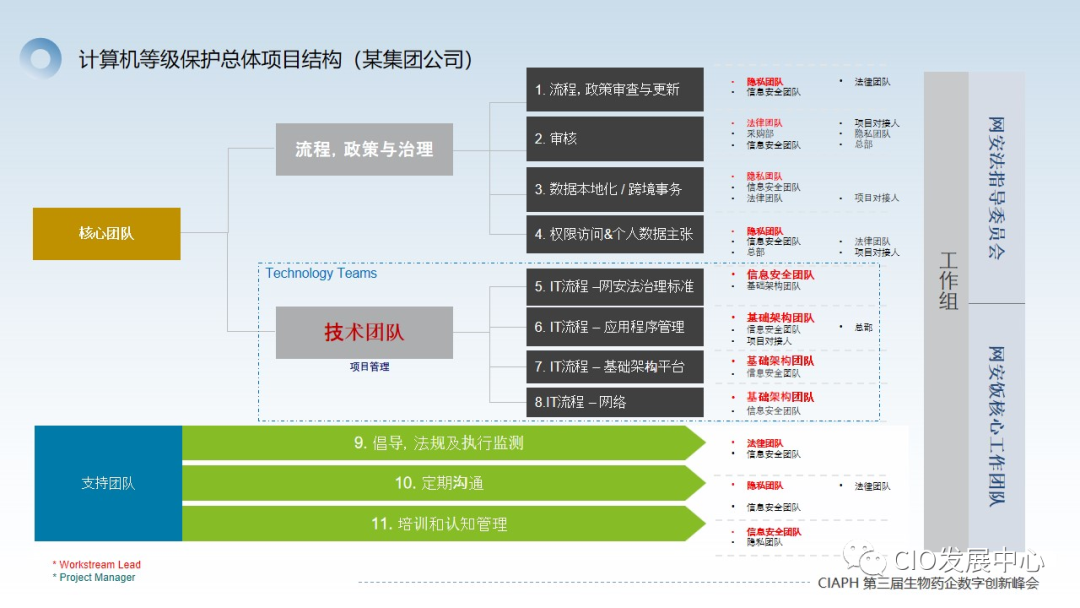
评估过程中,要看应用系统是否需要重构、优化或者升级,要有不同的团队支持,最后要做漏洞扫描、渗透测试,基于产生的结果再进行整改,最终进行验证出证。一套流程下来大概需要几个月时间。一般对于一个中型企业汇总下来大概会有几十套应用程序,从评估、迁移整改,到预认证、等级保护认证,想要成功做好等级保护,需要跨部门的合作以及相应的投入。 数字化转型网(www.szhzxw.cn)

在跨境数据传输场景中,企业需要对数据进行梳理并向网信办上报,随后根据反馈意见进行修改和完善。尽管这一过程可能相对漫长和反复,企业需要投入了大量人力,但它带来的好处在于内部数据得到更清晰的梳理,降低了应用存在的潜在风险。另外根据国家颁布的法规要求,可以更有效地保护数据,根据不同类型的数据,执行相应的指导建议以达到不同的保护等级。同时借助这个机会优化许多历史遗留的老系统,使整个IT管理更加精炼。从积极的角度来看,这对企业内部的IT部门是非常有帮助的。
第二个案例涉及终端数据防泄漏,这在内控领域扮演着关键角色。我们需要制定一些策略来规范上网行为、防范异常打印、敏感数据拷贝等风险。在发现异常时,我们希望能够让合规部门或商密部门第一时间了解,并采取相应行动,这需要借助一些专业工具的支持。图中左侧展示了一些常见问题,而右侧则呈现了企业管理层期望达到的效果。尽管上云变得更为便利,但模糊的边界使得防范工作变得更加复杂。在面对诸多可能导致数据泄漏的场景时,我们通过终端数据防泄漏的方法,旨在确保用户在使用电脑时不会将敏感数据泄露给外部或他人,从而统一方法,防止数据流失。因为数据流失可能意味着公司资产的损失。

总体而言,通过数据防泄漏方案我们可以设定一些预置条件,如规定聊天内容、U盘文件拷贝、打印机密文件以及邮件发送敏感内容等。这些条件可以通过动态感知和智能拦截的技术手段实施,对公司的信息安全管理是非常有利的。 数字化转型网(www.szhzxw.cn)
最后分享一些个人心得。在信息安全领域,我们需要找到一种平衡状态,使信息安全更好地融入业务体系,既不会让员工忽视信息安全的存在,又能保持一定的神秘感。因此,对员工的培训至关重要,要确保他们了解什么是应该做的,什么是不应该做的。许多情况下员工泄漏信息是无意的行为,可以通过强化培训,提高他们的认知水平,并借助一些技术工具全面提高信息安全防护水平。
在推进信息安全实践中,我认为有以下一些点需要大家特别注意:
- 制定信息安全策略,针对于矛和盾,勇于质疑和挑战来提高。
- 必须要结合业务,学会和业务对话,了解企业环境中存在哪些风险,创造价值并与执行层沟通。
- 预算支持的挑战:信息安全是一个难以获得预算支持的项目,因为其实际效果难以直观展示。因此,成功实施信息安全需要获取管理层的资金支持和执行支持。
- 了解法规需求:需要充分了解法律法规的最新要求,整个信息安全项目要与合规部门、法律部门,甚至是业务部门共同协作,以制定新的标准。
- 工具选择的智慧:在选择工具时要做到“选对的,而不是选贵的”。必须通过多轮评估确定在当前企业环境中最适合落地的技术。 数字化转型网(www.szhzxw.cn)
- 员工理解与参与度:员工的理解和参与度至关重要。信息安全既不能使员工过度猜忌,同时也不能暴露所有底牌,最佳状态是保持若即若离的平衡。
- 积极参与行业交流:积极参与行业内外的交流,包括外部会议和内部学习分享,是提升认知的有效手段。面对困难时,积极寻求沟通和帮助是必不可少的。
以上内容就是我想为大家分享的,希望我的经验能够给大家带来一些思考和帮助,谢谢。

翻译:
Prepare for a rainy day: New trends and countermeasures of information security in pharmaceutical industry
This article is shared by CIAPH according to Meng Wei, former information technology Director of West ‘an Janssen, at the “CIAPH Third Digital Innovation Summit for biological pharmaceutical Companies and into Jingtai Technology” event.
With the advancement of the digital era, data information has injected a strong impetus into all walks of life and provided strong support for various fields. However, with that comes increasing data security risks. The information infrastructure in the pharmaceutical industry is not the same as in other fields, because it is directly related to people’s lives. Data in this area has special properties that make it a focus for attackers. 数字化转型网(www.szhzxw.cn)
At the “CIAPH Third Biologic pharmaceutical Company Digital Innovation Summit and into Jingtai Technology” event, Meng Wei, former Director of information technology of Xi ‘an Janssen, shared how to deal with the new trend of information security in the pharmaceutical industry from his personal experience, and also brought actual cases, the following is the details.
Meng Wei is the former information technology Director of Xi ‘an Janssen
Hello, everyone, I’m Meng Wei. With the continuous development of the Internet, cloud computing and artificial intelligence, digital transformation brings new security challenges for enterprises. In the pharmaceutical industry, the importance of information security issues has become increasingly prominent. Therefore, today I will take information security as the theme, share my practice and experience in this field in recent years, and discuss with you.
In the past, when we talked about information security, we focused on how to effectively manage networks, ensure the security of data transmission, and strengthen encryption measures. However, as technology continues to evolve, information security has evolved into a broader concept that includes compliance management, integration with the business, and even governance and regulation involving artificial intelligence, as well as the normalization of behavior within the enterprise. At present, enterprises are frequently threatened by the blackmailer virus, so how to prevent such threats needs to work together from many aspects such as ideology, technology, and process to prevent the occurrence of security risks.
In general, it is important for enterprises to understand their own strengths and weaknesses and industry experience in formulating security strategies and resisting risks. It is recommended to regularly communicate with peers in the industry and maintain communication with partners. In order to properly evaluate reasonable information security solutions. Especially after the release of the “Network Security Law” and the “Personal Information Protection Law”, it is necessary to comprehensively comb all the data of the enterprise in the first time to understand the storage location and role of the data, which is crucial for follow-up measures. Only with a sufficient understanding of the data can private and sensitive data be processed quickly, and the work of improvement and collation will be smoother. In addition, enterprises should carry out hierarchical protection and encryption of data through technical means. When employees use data, make sure the organization has clear processes and rules and regulations to prevent leakage due to improper access. Therefore, effective methods are needed to prevent data loss and leakage. Finally, through a series of governance principles, data is comprehensively controlled, from technical means to terminal control, to achieve data security protection in the whole process.
When enterprise informatization develops to a certain stage, it is necessary to establish a complete data security governance framework. Here’s a quick rundown of the process:
First, determine the goals that are appropriate for the development stage of the enterprise. These goals can cover areas such as security, integrity, availability, compliance, and risk management.
Personnel involvement: In order to achieve the set goals, there needs to be the corresponding personnel participation, and even a special team can be set up to be responsible. Part-time participation is also possible for small IT teams; For large IT teams, it is best to set up a dedicated security position.
Develop security policies and processes: Establish a set of security policies and processes to give the entire enterprise a clear understanding of how to protect data.
Select technologies and tools: Find the right technologies and tools, such as backup, leak protection, and encryption. Make sure you have a dedicated colleague in charge to avoid confusion when different databases use different technologies. Once strategy and technology are aligned, management becomes easier. 数字化转型网(www.szhzxw.cn)
Employee training: In the field of security, security is not only a matter for the IT department, but should be the responsibility of the entire enterprise. Therefore, employee training is critical and needs to cover both front-line personnel and management.
Compliance with laws and regulations: In the face of ever-increasing laws and regulations, it is necessary to ensure corporate compliance. Violations of regulations not only affect the company’s reputation, but can also result in fines and have an adverse impact on the financial statements of the company.
In today’s share, I bring you two cases.
First, we share the content of network security law and computer level protection. With the continuous deepening of digitalization, we find that not only in the IT field, but also in the business departments, R&D departments and other departments besides IT, are increasingly paying attention to security issues. As we can see from the project architecture of the case study, moving forward with a national computer level protection project requires the collaboration of many teams, as well as the consideration of key functions at headquarters, which may have an impact on data, architecture, technology, as well as existing marketing and research and development programs. In general, obtaining a national grade protection certification is a process, and not a permanent one. For example, if it is a secondary insurance, it needs to be declared every two years, while a tertiary insurance needs to be declared once a year. Of course, these work need to have the corresponding cost support, so in the early stage of the project, we must carefully consider whether there is enough budget to support this process, data security should not be just an empty word, the real implementation needs to be supported by the boss and the company’s management, because every step of the action needs funds to provide protection. It’s nothing without a budget. 数字化转型网(www.szhzxw.cn)
In the evaluation process, it is necessary to see whether the application system needs to be restructured, optimized or upgraded, to have different team support, and finally to do vulnerability scanning, penetration testing, based on the resulting results and then rectification, and finally verification. A process can take months. Generally, for a medium-sized enterprise, there will be dozens of sets of applications, from assessment, migration and rectification, to pre-certification, grade protection certification, and to successfully do grade protection, cross-departmental cooperation and corresponding investment are needed.
In the cross-border data transfer scenario, enterprises need to sort out the data and report it to the Cyberspace Administration, and then modify and improve it based on feedback. Although this process can be relatively long and iterative, requiring a lot of manpower, the benefit is that the internal data is more clearly combed, reducing the potential risks of the application. In addition, according to the regulations issued by the state, data can be more effectively protected, and according to different types of data, the corresponding guidance and recommendations are implemented to achieve different levels of protection. At the same time, take advantage of this opportunity to optimize many legacy systems and make the overall IT management more refined. On a positive note, this can be very helpful to IT departments within the enterprise. 数字化转型网(www.szhzxw.cn)
The second case involves terminal data leakage prevention, which plays a key role in the field of internal control. We need to develop some policies to regulate online behavior, prevent abnormal printing, sensitive data copy and other risks. When anomalies are found, we hope to let the compliance department or business security department know about them at the first time and take corresponding actions, which requires the support of some professional tools. The left side of the graph shows some common problems, while the right side shows what the management wants to achieve. While access to the cloud has become easier, the blurring of boundaries has made prevention more complicated. In the face of many scenarios that may lead to data leakage, we use the terminal data leakage prevention method to ensure that users will not leak sensitive data to the outside or others when using the computer, so as to unify the method and prevent data loss. Because the loss of data can mean the loss of company assets.
In general, we can set some preset conditions through the data leak prevention program, such as specifying chat content, copy of USB flash drive files, print confidential files, and email sensitive content. These conditions can be implemented through the technology of dynamic perception and intelligent interception, which is very beneficial to the information security management of the company.
Finally, share some personal insights. In the field of information security, we need to find a balance state, so that information security is better integrated into the business system, not to let employees ignore the existence of information security, but also to maintain a certain sense of mystery. Therefore, the training of employees is crucial to ensure that they understand what should and should not be done. In many cases, employees’ leakage of information is unintentional behavior. Through intensive training, we can improve their cognitive level and comprehensively improve the level of information security protection with the help of some technical tools. 数字化转型网(www.szhzxw.cn)
In promoting the practice of information security, I think there are some points that need to be paid special attention to:
Develop an information security strategy, aiming at spear and shield, dare to question and challenge to improve.
You have to connect with the business, learn to talk to the business, understand what risks exist in the enterprise environment, create value and communicate with the executive level.
Budget support challenges: Information security is a difficult project to get budget support for, because its actual effects are difficult to visualize. Therefore, successful implementation of information security requires financial support and executive support from management.
Understand regulatory requirements: It is necessary to fully understand the latest requirements of laws and regulations, and the entire information security project needs to work with the compliance department, the legal department, and even the business department to develop new standards.
The wisdom of tool selection: Choose the right tool, not the expensive one. Multiple rounds of evaluation must be conducted to determine the most suitable technology for implementation in the current enterprise environment. 数字化转型网(www.szhzxw.cn)
Employee understanding and engagement: Employee understanding and engagement are critical. Information security can neither make employees overly suspicious, but also can not expose all the cards, the best state is to maintain a balance of ambiguity.
Active participation in industry exchanges: Active participation in internal and external industry exchanges, including external meetings and internal learning sharing, is an effective means of raising awareness. When facing difficulties, it is essential to actively seek communication and help.
The above content is what I want to share with you. I hope my experience can bring you some thinking and help. 数字化转型网(www.szhzxw.cn)
本文由数字化转型网(www.szhzxw.cn)转载而成,来源于CIO发展中心,作者老杨;编辑/翻译:数字化转型网宁檬树。

免责声明: 本网站(http://www.szhzxw.cn/)内容主要来自原创、合作媒体供稿和第三方投稿,凡在本网站出现的信息,均仅供参考。本网站将尽力确保所提供信息的准确性及可靠性,但不保证有关资料的准确性及可靠性,读者在使用前请进一步核实,并对任何自主决定的行为负责。本网站对有关资料所引致的错误、不确或遗漏,概不负任何法律责任。
本网站刊载的所有内容(包括但不仅限文字、图片、LOGO、音频、视频、软件、程序等) 版权归原作者所有。任何单位或个人认为本网站中的内容可能涉嫌侵犯其知识产权或存在不实内容时,请及时通知本站,予以删除。