摘 要:
构建以数据产权为基础的数据要素基础制度体系,其基本要旨是为了统筹推进流通交易、收益分配、安全治理协同发展的数据要素市场,更好地协调和处理与数据生产力发展相适应的数字化生产关系。数据流通与交易制度应体现高效与合规,数据要素收益分配制度应体现效率与公平,数据要素治理制度要坚持安全与发展并重,构建政府、企业、社会多方协同治理模式。
关键词:数据流通;数据交易;数据收益分配;数据治理
一、数据全流程合规与监管规则体系
数据是国家重要的战略性资源,任何组织和个人开展数据处理活动必须遵守法律和法规。目前,数据监管领域涉及的法律法规主要包括《网络安全法》《数据安全法》《个人信息保护法》《关键信息基础设施安全保护条例》《网络数据安全管理条例》以及省、自治区、直辖市人大及其常委会制定和公布的地方性数据法规等。
2017年6月1日正式施行的《网络安全法》在国际网络安全严峻时期出台,为我国有效应对网络与数据安全威胁和风险,全方位保障网络与数据安全提供了坚实的法律保障。《网络安全法》是我国第一部既涉及网络安全,又涉及数据安全和个人信息保护的网络与数据领域的综合性和基础性立法。在数据保护方面,《网络安全法》重点规定了数据分类、重要数据备份和加密等措施,重要数据的境内存储和出境安全评估制度,维护网络数据的完整性、保密性和可用性,以及确立了网络数据的定义等。
2021年9月1日起实施的《数据安全法》第二十七条规定,数据处理者开展数据处理活动应当依照法律、法规的规定,并依照法律法规,建立健全全流程数据安全管理制度,组织开展数据安全教育培训,采取相应的技术措施和其他必要措施,保障数据安全。利用互联网等信息网络开展数据处理活动,应当在网络安全等级保护制度的基础上,履行上述数据安全保护义务。如果是重要数据的处理者,应当明确数据安全负责人和管理机构,并落实数据安全保护责任。 数字化转型网www.szhzxw.cn
《数据安全法》确立了“建立健全全流程数据安全管理制度”的全流程安全法律制度,与《数据安全法》同日实施的《关键信息基础设施安全保护条例》第六条要求,运营者应当依照本条例和有关法律、行政法规的规定以及国家标准的强制性要求,在网络安全等级保护的基础上,采取技术保护措施和其他必要措施,应对网络安全事件,防范网络攻击和违法犯罪活动,保障关键信息基础设施安全稳定运行,维护数据的完整性、保密性和可用性。
《个人信息保护法》明确规定,处理个人信息应遵循合法、正当、必要和诚信原则,并在总则部分第六条提出了两个“最小原则”,即采取对个人权益影响最小的方式,限于实现处理目的的最小范围。《个人信息保护法》的两个“最小原则”是处理个人信息应遵循的核心原则,尤其是处理目的的“最小范围”,这是禁止“过度收集个人信息”的关键要点,因为个人信息处理者只有在严格遵守处理目的的“最小范围”的前提下,即“非必要不收集”的情况下,才能确保其采取对个人权益影响最小的方式。
《网络数据安全管理条例》则要求,任何个人和组织开展数据处理活动应当遵守法律、行政法规,尊重社会公德和伦理,不得从事以下六类活动,一是危害国家安全、荣誉和利益,泄露国家秘密和工作秘密;二是侵害他人名誉权、隐私权、著作权和其他合法权益等;三是通过窃取或者以其他非法方式获取数据;四是非法出售或者非法向他人提供数据;五是制作、发布、复制、传播违法信息;六是法律、行政法规禁止的其他行为。
数据要素流通和交易必须在安全合规和有效监管的基础上进行,这需要构架全国统一的数据要流通和交易全流程合规与监管规则体系,重点强化市场主体在数据流通和交易全流程合规治理体系的构建,首先,要确保流通的数据来源合法,根据《数据安全法》的规定,开展数据处理活动,应当遵守法律、法规,尊重社会公德和伦理,遵守商业道德和职业道德,诚实守信,履行数据安全保护义务,承担社会责任,不得危害国家安全、公共利益,不得损害个人、组织的合法权益;其次,确保数据交易规范合规,数据交易标的规范合规主要指数据供方交易的数据获取渠道合法、权利清晰无争议,能向数据交易机构提供拥有交易数据完整相关权益的承诺及交易数据采集渠道、个人信息保护政策、用户授权等相关材料,以及确保交易数据的真实性,能够向数据交易机构提供交易数据真实性的承诺及相关材料。数据交易机构或其委托的合法数据处理机构应当对数据供方提供的交易数据的合法、真实、来源进行合规审查;再次,确保敏感个人信息得到充分保护,根据《个人信息保护法》的规定,敏感个人信息一旦泄露或者非法使用,容易导致自然人的人格尊严受到侵害或者人身、财产安全受到危害,主要包括生物识别、宗教信仰、特定身份、医疗健康、金融账户、行踪轨迹等信息,以及不满十四周岁未成年人的个人信息
二、统筹构建规范高效的
数据交易场所数据交易场所的构建应当要体现交易制度的公平合规与运行机制的有序高效。“数据二十条”提出:“完善和规范数据流通规则,构建促进使用和流通、场内场外相结合的交易制度体系”。场内交易是指在数据交易所内,按一定规则进行的交易;场外交易,即在数据交易所之外,双方依法自行的交易行为。我国具有代表性的两部地方性数据综合性立法——《深圳经济特区数据条例》和《上海市数据条例》均规定,市场主体可以通过依法设立的数据交易(所)平台进行数据交易,也可以由交易双方依法自行交易。 数字化转型网www.szhzxw.cn
目前,数据的场外交易比较活跃,场内数据交易相对冷淡,而违法的黑市数据交易已形成相当规模,主要涉及个人信息,特别是与敏感个人信息相关的个人信息,严重侵犯公民的个人信息。2019年至2022年10月,全国检察机关共批准逮捕涉嫌侵犯公民个人信息犯罪嫌疑人1.3万余人,提起公诉2.8万余人。从最高人民检察院2022年发布的5件侵犯公民个人信息犯罪典型案例看,主要涉及对敏感个人信息的侵犯,包括公民征信信息、生物识别信息、行踪轨迹信息、健康生理信息等。
在个人数据的交易层面,有学者认为“个人数据交易一级市场应遵循告知同意原则,二级市场应遵循合法原则和兼容原则”,并提议对我国《个人信息保护法》第14条第2款、第22条、23条作相应修订。党的二十大报告强调要“加强个人信息保护”。笔者认为,无论数据的场内交易,还是场外交易,应当严格禁止涉及非经个人授权同意的个人信息交易,尤其是敏感个人信息的交易,但是个人信息经过匿名化处理的除外。鉴于数据资产交易处在培育期,应严格依法规范数据的场外交易,逐步由场外交向场内交易过渡,在依法设立的数据交易机构进行交易,严厉打击数据的黑市交易,营造安全可信有序的数据交易市场环境。
根据《数据安全法》第三十四条规定,法律、行政法规规定提供数据处理相关服务应当取得行政许可的,服务提供者应当依法取得许可。鉴于数据交易标的和行为的特殊性,从事数据交易机构的准入,应当依据《行政许可法》第十二条规定设立行政许可制度。据了解,我国已建成近40家数据交易所,多数数据交易所存在同一地区内重复建设、数据割据和无序竞争现象。为此,“数据二十条”强调,要加强数据交易场所体系设计,统筹优化数据交易场所的规划布局,严控交易场所数量,建议由新组建的国家数据局整体规划和出台数据交易所整体规划和布局方案。
三、培育数据要素流通和交易服务生态
实现数据要素的安全高效流通和交易,需要构建数据流通和交易供应链服务生态体系。数据供应链交易生态服务体系包括数据提供方、购买方、平台方、监管方以及第三方中介服务方。这里最要的是构建数据要素流通和交易的三方中介服务生态体系,国家要培育一大批专业化、合规化、规模化的第三方数据要素专业服务机构,包括数据集成、数据经纪人、数据合规认证、数据安全审计、数据公证、数据保险、数据托管、数据资产评估、数据争议仲裁、数据交易风险评估、数据要素人才培训,以此极大地提升数据流通和交易全流程服务能力和体系。 数字化转型网www.szhzxw.cn
2022年5月,欧盟理事会批准通过《数据治理法案》(Data Governance Act,简称:DGA)。DGA强调规则创新,鼓励数据的共享和提高数据利用的效率,让数据资源的流转利用服务更高的公共政策目标:首先,建立公共部门持有数据的再利用机制;其次,建立框架以促进数据中介机构的发展;再次,对于数据利他行为做出规范化的引导。在促进数据利用方面,DGA尤其强调了数据中介的作用,建立如数据商店、数据经纪人、数据信托等数据流通和交易等数据中介服务模式。事实上,实现安全可信高效的数据流通和交易,数据经纪人和数据安全合规认证中介服务的功能和作用非常重要。
数据经纪商(Data Broker)与“数智”时代的数据经纪人的服务内容完全不同,根据美国联邦贸易委员会(Federal Trade Commission,FTC)的定义,数据经纪商是通过各种渠道采集消费者个人信息,并对采集的原始信息及衍生信息进行整理、分析和分享后,向与消费者没有直接关系的企业出售、许可、交易或提供该信息,用于产品营销、验证个人身份或检测欺诈行为等;“数智”时代,数据经纪人绝不仅仅是通过各种渠道采集消费者个人信息和数据交易的撮合服务功能,现代数据经纪人服务的主要功能,包括大量的数据增值服务包括进行数据收集、汇聚、处理、加工,同时要提供算法,提供数据存储,提供计算算力,提供流通保障技术环境,以及提供围绕数据交易和流通的相关咨询和代理服务等。
数据合规认证是保证数据要素安全高效流通和交易的合规认证中介服务,主要是对数据安全合规的认证。根据《数据安全管理认证实施规则》,数据安全管理认证的认证模式包括:技术验证+现场审核+获证后监督,其中技术验证要求第三方技术验证机构按照认证方案实施数据安全技术验证,并向认证机构和认证委托人出具技术验证报告。技术验证机构按照认证方案实施数据安全技术验证,重点开展数据流通和交易活动的安全风险监测,发现数据安全缺陷、漏洞等风险时,应责成采取加密、脱敏、备份、访问控制、审计等技术或者其他必要措施。加强在数据流通和交易中的数据安全防护,保护数据免受泄露、窃取、篡改、损毁、不正当使用等;对重要数据和敏感个人信息进行重点保护,应按照规定对其数据处理活动定期开展风险评估,并向有关主管部门报送风险评估报告。风险评估报告应包括处理的重要数据的种类、数量,开展数据处理活动的情况,面临的数据安全风险及其应对措施等。同时,要应建立数据安全管理责任和评价考核制度,制定数据安全保护计划,开展安全风险评估,组织开展数据安全合规教育培训等。认证机构应当在认证有效期内,对获得认证的网络运营者进行持续监督,并合理确定监督频次,确保数据流通和交易的安全与合规。
四、数据资产的认定与评估
数据要素的价格确定,本身是数字经济发展过程中所面临的一个难题。如果允许自由定价,那么数据所有者或者控制者可以设置一个非常高的许可价格,使数据作为核心要素失去意义。因此,数据要素的价格除了数据供需双方之间进行议价交易外,一般需要通过建立数据资产评估机制和制定数据价值评估准则进行认定。
我国《资产评估法》对“资产评估”给出的定义是:“评估机构及其评估专业人员根据委托对不动产、动产、无形资产、企业价值、资产损失或者其他经济权益进行评定、估算,并出具评估报告的专业服务行为。”《财政部关于修改<企业会计准则——基本准则>的决定》关于“资产”的定义是,资产是指企业过去的交易或者事项形成的、由企业拥有或者控制的、预期会给企业带来经济利益的资源。首先,企业过去的交易或者事项包括购买、生产、建造行为或其他交易或者事项。预期在未来发生的交易或者事项不形成资产;其次,由企业拥有或者控制,是指企业享有某项资源的所有权,或者虽然不享有某项资源的所有权,但该资源能被企业所控制;再次,预期会给企业带来经济利益,是指直接或者间接导致现金和现金等价物流入企业的潜力。可见,资产的形成具有三大特征,一是已经发生或形成的交易或者事项;二是由企业拥有或者控制;三是预期会给企业带来经济利益。 数字化转型网www.szhzxw.cn
2022年,国家知识产权局决定在浙江、上海、深圳等地开展数据知识产权保护试点,力争在立法、存证登记等方面取得可复制可推广的经验做法,为后续制度设计提供实践基础。2023年“两会”期间,国家知识产权局副局长何志敏建议,借鉴以无形财产为客体的知识产权法律制度,尽快建立数据知识产权制度。根据《资产评估准则——无形资产》对“无形资产”的认定,即特定主体所拥有或者控制的,不具有实物形态,能持续发挥作用且能带来经济利益的资源。《国际会计准则第38号无形资产》(IAS38)将“无形资产”定义为:用于商品或劳务的生产或供应、出租给其他单位、或管理目的而持有的、没有实物形态的、可辨认非货币资产。我国《企业会计准则第6号——无形资产》对无形资产的定义是:企业拥有或者控制的没有实物形态的可辨认非货币性资产。从国际会计准则和我国企业会计准则关于“无形资产”的定义可已看出,无形资产的基本特征是“可辨认性”。但是,数据资产不完全符合会计准则中“无形资产”的定义,既不同于传统的不动产、动产,也不同于类似知识产权没有实物形态的可辨认非货币性资产。数据资产主要是以数据为载体和表现形式,而且能够进行计量,并能带来直接或者间接经济利益的数据资源。数据资产通常包括三大基本属性,即通用属性、业务属性和管理属性:一是通用属性,主要包括数据来源、数据类型、数据结构、时段、更新周期、元数据和存储形式等;二是业务属性,包括业务描述、业务模型、业务规则和关联关系等;三是管理属性,包括数据分类分级、安全信息、数据溯源、职责权限和应用场景等。因此,数字资产的评估应当基于数字资产的基本属性,重点聚焦对数据价值的评价,包括数据产生的质量要素、成本要素、应用价值等。从数字资产的整体性考虑,主要的权重则是数据资产的质量要素和应用价值。
首先,数据质量要素主要包括:安全性、真实性、准确性、一致性、完整性、规范性、时效性和合规性等。上述数据质量要素中最重要的是四个要素,一是安全性,即数据不涉及国家安全、企业商业秘密以及个人隐私信息等;二是真实性,即数据在信息系统中能准确表示其所描述事物的真实性,确保数据的真实性是数据资产评价的第一要务;三是规范性,即数据资产符合数据标准,这里的标准不能简单地理解为数据要素领域所需要统一的技术要求,而是评价数据价值在内外部使用和交换过程中保持一致性和准确性的一系列规范性约束;四是合规性,即数据权属、数据权限、数据分类、数据安全、侵权救济,以及数据的许可使用、质押、转让、仲裁等。
其次,数据资产的应用价值主要包括使用范围、应用场景、商业模式、供求关系、数据关联性和应用风险等。使用范围应关注数据资产涉及的行业、领域和区域等;应用场景应关注数据资产的使用方式、开放程度和使用频率等;商业模式应关注数据产品及服务的模式、赋能模式和金融模式等;供求关系应关注数据资产的稀缺性、市场规模和价值密度等;数据关联性应关注数据资产的用户关联性、数间关联性和业务关联性等;应用风险应关注数据资产的管理风险、流通风险、数据安全风险、敏感性风险和监管风险等。在进行数据资产价值评估时,应分析数据资产的应用要素。
五、构建安全合规的数据跨境流通机制
数据的流通不仅限定在国内,数据的流通具有全球性。跨越国境的国际贸易交易,无论是进口贸易,还是出口贸易均需要附带数据的跨境传输。目前,数据跨境流动,主要是因商业和生产的需要确需向境外提供数据,很少把数据本身作为商品跨境交易。然而,数据的跨进传输已经从原来的“如何传输”,进入了“如何可信安全传输”的时代,安全合规有序的数据跨境双向流动机制的构建,对于跨境贸易交易具有极其重要的作用。 数字化转型网www.szhzxw.cn
数据出境的安全问题不仅关乎数据本身作为重要生产要素的开发利用与安全问题,还与国家主权、国家安全、个人信息权益、社会公共利益等休戚相关。为此,“数据二十条”要求,对影响或者可能影响国家安全的数据处理、数据跨境传输、外资并购等活动依法依规进行国家安全审查。数据安全审查制度是《数据安全法》确立的一项重要国家安全审查制度,2022年2月新修订的《网络安全审查办法》第十条的规定,网络安全审查重点评估相关对象或者情形的以下国家安全风险因素:(一)产品和服务使用后带来的关键信息基础设施被非法控制、遭受干扰或者破坏的风险;(二)产品和服务供应中断对关键信息基础设施业务连续性的危害;(三)产品和服务的安全性、开放性、透明性、来源的多样性,供应渠道的可靠性以及因为政治、外交、贸易等因素导致供应中断的风险;(四)产品和服务提供者遵守中国法律、行政法规、部门规章情况;(五)核心数据、重要数据或者大量个人信息被窃取、泄露、毁损以及非法利用、非法出境的风险;(六)上市存在关键信息基础设施、核心数据、重要数据或者大量个人信息被外国政府影响、控制、恶意利用的风险,以及网络信息安全风险;(七)其他可能危害关键信息基础设施安全、网络安全和数据安全的因素。
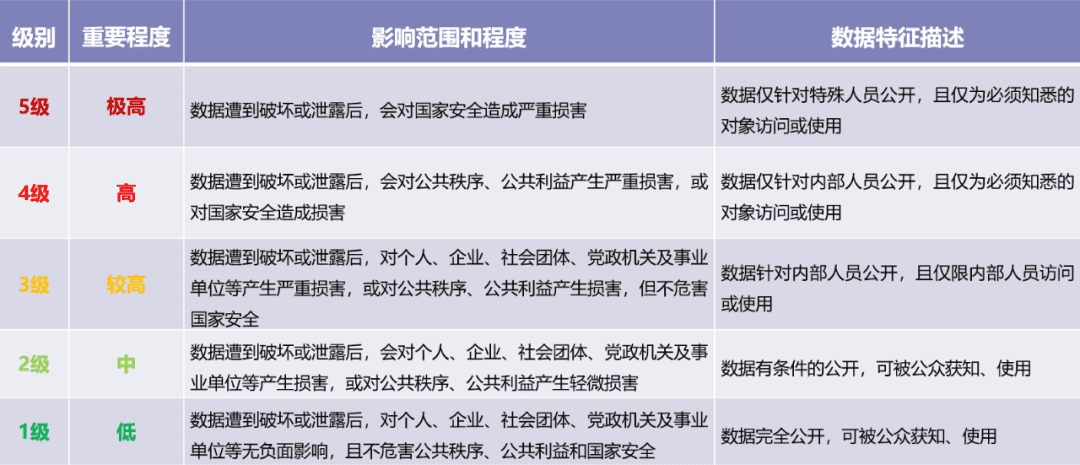
《网络安全审查办法》第十条(五)(六)主要是针对核心数据、重要数据或大量个人信息被窃取、泄露、毁损以及非法利用、非法出境的风险,以及上市存在关键信息基础设施、核心数据、重要数据或者大量个人信息被外国政府影响、控制、恶意利用的风险等。目前,我国数据立法将数据分为一般数据、重要数据、核心数据,这个数据分类的方法主要是基于数据对国家安全、公共利益或者个人、组织合法权益的影响和重要程度。 数字化转型网www.szhzxw.cn
“数据二十条”要求,积极参与数据跨境流动国际规则制定,探索加入区域性国际数据跨境流动制度安排。2022年1月1日,《区域全面经济伙伴关系协定》(RCEP)正是对我国生效,这个历经8年谈判的RCEP在数据跨境流动方面做出了具体的规定。RCEP在第十二章第十五条要求:“任何缔约方不得阻止涵盖的人为进行商业行为而通过电子方式跨境传输数据”。同时,RCEP又强调:“该缔约方认为对保护其基本安全利益所必需的任何措施,其他缔约方不得对此类措施提出异议”。可见,RCEP将数据跨境自由流动作为一项基础性原则,但同时RCEP尊重一个主权国家为了国家安全利益,而实施对数据跨境流动的任何安全保护措施,这其中就包括了国家数据安全审查。
事实上,“数据二十条”将“数据跨境流动”作为一项基本原则,只是对影响或者可能影响国家安全的数据处理、数据跨境传输和外资并购等活动实施国家安全审查。“数据二十条”强调,坚持开放发展,推动数据跨境双向有序流动,鼓励国内外企业及组织依法依规开展数据跨境流动业务合作,支持外资依法依规进入开放领域,推动形成公平竞争的国际化市场。
目前,在北京数字贸易试验区、上海自由贸易试验区、浙江自由贸易试验区、海南自由贸易港均制订了数据跨境方案。建议在上述“自贸区”试点建设离岸数据中心,探索安全规范的跨境数据跨境流动方式,重点针对跨境电商、跨境支付、供应链管理、服务外包等典型应用场景。自由贸易试验区的离岸数据中心应当按照国际规则或惯例,实施一种特殊的互惠政策和制度安排,比如可以使用国际互联网专用通道,使自贸区内的国际数据传输与自贸区外相比,更加自由和便利,甚至可以不执行或不完全执行中国境内有关数据跨境的法律法规等。 数字化转型网www.szhzxw.cn
六、数据要素的初次分配与政府调节功能
党的十九届四中全会通过的《中共中央关于坚持和完善中国特色社会主义制度、推进国家治理体系和治理能力现代化若干重大问题的决定》(以下简称《决定》)提出,“健全劳动、资本、土地、知识、技术、管理、数据等生产要素由市场评价贡献、按贡献决定报酬的机制”。《决定》确立的数据要素采用“市场评价贡献、按贡献决定报酬的机制”,为构建体现效率与促进公平的数据要素收益分配制度指明了方向。对此,“数据二十条”再次加以强调,同时还提出要更好地发挥政府在数据要素收益分配中的引导调节作用。2023年3月,中共中央、国务院发布的《数字中国建设整体布局规划》进一步指出,要释放商业数据价值潜能,加快建立数据产权制度,开展数据资产计价研究,建立数据要素按价值贡献参与分配机制。
(一)引导数据要素的初次分配
数据本身并不能直接参与生产和分配,必须通过数据要素各参与方的投入将数据转化为有生产价值的数据要素。数据作为生产要素应当具备三大功能,一是数据生产要素能为经济的高速增长创造价值;二是数据生产要素与其他生产要素融合,具有放大和倍增作用;三是数据生产要素能参与收益分配。“数据二十条”提出,推动数据要素收益向数据价值和使用价值的创造者合理倾斜,确保在开发挖掘数据价值各环节的投入有相应回报,强化基于数据价值创造和价值实现的激励导向。
目前,应当重点关注和引导数据要素的初次分配,数据要素的初次分配是最基本、最基础、最直接的知识劳动创造价值的过程,要结合数据要素的特征,优化初次分配结构和权重。在数据要素的初次分配阶段,应当按照“谁投入、谁贡献、谁受益”原则,着重保护数据要素各参与方的投入产出收益,在提高数据利用效率的基础上,让数据处理者的劳动价值创造得到合理和公平的回报。这里要特别强调,要重视和提高数据处理者劳动报酬在初次分配中的比重,尤其是优化以知识价值为导向的数据要素收益分配政策,尊重数据要素各参与方的科研、技术、管理人才的作用,充分体现知识、管理、技术对数据要素市场的贡献。
保障高效和公平的数据要素收益分配体制机制,必须更好地发挥政府在数据要素收益分配中的引导调节作用。我国的数据要素市场处在培育期,数据要素收益分配制度尚未建立,仅凭市场机制是无法保证数据要素收益初次分配的公平性。因此,只有充分发挥政府在数据要素收益分配中的引导调节作用,才有可能实现数据要素收益初次分配的公平性。
(二)发挥政府在数据要素收益分配中的调节功能
在数字产业化和产业数字化发展进程中,为了避免大型数据企业对数据加以垄断,进而形成数据富有者和数据贫困者之间的“数据鸿沟”,规避数据贫富两极分化带来的不公平和风险,政府应当发挥在数据要素收益分配中的引导和调节作用。数据要素收益分配体制在强调效率优先的基础上,应当保证其分配的公平性,而仅仅通过数据要素市场的初次分配是很难实现,因此,必须发挥政府在数据要素收益再分配市场中的引导调节作用,推动大型数据企业积极承担社会责任,尽可能地缩小数据富有者和数据贫困者之间的“数据鸿沟”,将数据税收入向实体经济投入,尤其是向传统制造业数字化转型的行业倾斜,着重保障公平的数据要素收益分配体制。 数字化转型网www.szhzxw.cn
政府还应当倡导数据公益,更好地使用数据、挖掘数据、共享数据,为全社会公益创造更大的经济溢出效应,促进基本数据公共服务均等化。数据公益不是数据分配的均等主义,更不是削弱市场和政府对于数据要素的调配和监督作用,而是让数据要素价值惠及更多中小微企业和更广大的人民群众。因此,必须充分发挥数据要素的公益目的和作用,促进全体人民共享数据发展红利。
七、数据要素协同治理应体现全过程安全
数据要素的治理必须要坚持安全与发展并重、鼓励与规范并举的原则,健全安全可控、弹性包容的数据要素治理规则体系,既要遵循安全可信,又要体现弹性包容。首先,要把安全贯穿数据治理全过程,数据安全是国家安全的重要组成部分。数据安全与国家政治安全、经济运行、社会治理、公共服务、国防安全、文化安全等方面密切相关;其次,要构建多方协同参与的治理模式,创新政府治理方式,明确各方主体责任和义务,完善行业自律机制,规范市场发展秩序,形成有效市场和有为政府相结合的弹性包容的数据要素治理格局。
(一)“数据要素治理”体系应平衡创新与监管
“数据要素治理”体系是数据要素四大基础制度体系的压舱石,“数据产权、流通交易、收益分配”制度是建立在数据治理基础上的三大支柱,没有安全可信有序的“数据要素治理”体系就没有数据的流通和交易,就无法保障数据要素各参与方的数据权益。 数字化转型网www.szhzxw.cn
“数据二十条”要求,充分发挥政府有序引导和规范发展的作用,守住安全底线,明确监管红线,打造安全可信、包容创新、公平开放、监管有效的数据要素市场环境。数据要素市场的发展是一个“创新—监管—再创新”的过程,其底层逻辑是创新和安全两种价值的平衡。首先,追求包容创新,要以宽容的心态接纳有瑕疵的创新,构建包容创新的容错纠错机制,这样数据要素市场的发展才有强劲的动力;其次,保障安全可信,安全和可信是相辅相成的,可信并不等同于安全,但可信是安全的基础,没有可信作为保障,安全将无从谈起,数据要素市场的发展应当建立在可信基础上的安全。
数据要素市场的良性发展,决不能脱离监管谈创新。鉴于数据非竞争性产生的巨大潜在的数据价值,为防范大型平台企业垄断数据,以及通过技术和资本优势排除竞争等不当行为,应尽可能地鼓励数据的广泛使用,保障公平竞争。近年来,一些大型互联网平台企业滥用市场支配地位、开展不正当竞争,导致“大数据杀熟”、限定交易等涉嫌垄断行为屡见不鲜。2021年11月实施的《个人信息保护法》专门规定要求平台企业履行“守门人”角色,并承担更多的社会责任,主要包括:应按照国家规定建立健全个人信息保护合规制度体系;成立主要由外部成员组成的独立机构进行监督;遵循公开、公平、公正的原则制定平台规则;对严重违法处理个人信息的平台内产品或服务提供者停止提供服务;定期发布个人信息保护社会责任报告并接受社会监督等。2022年6月,十三届全国人大常委会第三十五次会议表决通过了全国人大常委会关于修改《中华人民共和国反垄断法》的决定,于2022年8月1日起正式施行。新修订的《反垄断法》在第一条立法目的中明确提出“鼓励创新”,同时规定,具有市场支配地位的经营者不得利用数据和算法、技术以及平台规则等从事前款规定的滥用市场支配地位行为。对此,“数据二十条”也明确要求,企业应严格遵守反垄断法等相关法律规定,不得利用数据、算法等优势和技术手段排除、限制竞争,实施不正当竞争。
当然,数据要素市场的良性发展,也不能抑制创新谈监管,创新是数据要素市场发展的动力,监管是数据要素市场发展的安全保障,两者辩证统一、相互关联。数据要素市场的建立健全和良性发展,应当坚持促进发展和监管规范两手抓、两手都要硬,这就要求发挥政府有序引导和规范发展的作用,使数据要素市场在引导中规范、在规范中发展。要健全数据要素市场准入制度、公平竞争审查制度、公平竞争监管制度,建立全方位、多层次、立体化的监管体系,实现事前事中事后,全链条、全领域的数据要素市场监管体系,形成公平开放与有效监管相融合的数据要素市场环境。
(二)强化数据要素市场的协同治理
数据要素治理是逐步实现数据要素价值创造和构建数据要素市场良好秩序的过程。这需要“系统探究多元主体参与数据要素价值化过程的生态系统联动机制”,这是一个“多元主体协同共创”的过程。“数据二十条”提出,要充分发挥社会力量多方参与的协同治理作用。笔者认为,社会力量多方参与的协同治理,主要集中于三大协同治理主体:政府、企业和社会,其中政府的作用是监管、企业的义务是履责、社会的功能是监督。首先,要确立数据要素安全治理的关键制度,划定数据要素流通和利用的安全基线;其次,要构建多元主体协同共治的格局,着力提升数据要素市场的信任体系。
“数据二十条”提出,要建立数据要素市场信用体系,逐步完善数据交易失信行为认定、守信激励、失信惩戒、信用修复、异议处理等机制。2022年1月,国务院办公厅发布的《要素市场化配置综合改革试点总体方案》强调,要强化反垄断和反不正当竞争执法,规范交易行为,将交易主体违法违规行为纳入信用记录管理,对严重失信行为实行追责和惩戒。同时,要开展要素市场交易大数据分析,建立健全要素交易风险分析、预警防范和分类处置机制。鼓励建设和发展数据登记、数据价值评估、数据合规认证、交易主体信用评价等第三方服务机构,构建和完善数据要素市场服务体系。 数字化转型网www.szhzxw.cn
“数据二十条”专门提及,“加快推进数据管理能力成熟度国家标准及数据要素管理规范贯彻执行工作,推动各部门各行业完善元数据管理、数据脱敏、数据质量、价值评估等标准体系。”这里的“数据管理能力成熟度国家标准”是指我国首个数据管理领域的国家标准,全称为:《数据管理能力成熟度评估模型》GB/T36073-2018(简称:DCMM)“数据二十条”之所以要求加快推进DCMM的贯彻执行,是基于DCMM作为首部数据管理能力成熟度的国家标准,详细定义了数据战略、数据治理、数据架构、数据应用、数据安全、数据质量、数据标准和数据生存周期8个核心能力域,并细分为28个过程域和445条能力等级标准,确立了比较先进的数据管理理念和方法。
DCMM的评估模型将数据管理能力成熟度划分为五个等级,一级为初始级、二级为受管理级、三级为稳健级、四级为量化管理级、五级为优化级,这五个等级是递进关系,自低向高一级比一级深入,不同等级代表企业数据管理和应用成熟度水平的差异。DCMM的管理理念和评估模型不仅可以帮助企业建立和评价自身数据管理能力,持续完善数据管理组织、程序和制度,还可以加强数据要素在促进企业数字化和智能化转型过程中的数据管理制度创新和价值创造。
结语
2023年3月10日,十四届全国人大一次会议表决通过了关于国务院机构改革方案的决定,新增的国家数据局获得通过,正式开始组建。国家数据局属于国家发展和改革委员会管理的国家局。从国务院机构改革方案可以看出,新组建的国家数据局主要任务有三大类:一是负责协调推进数据基础制度建设;二是统筹数据资源整合共享和开发利用;三是统筹推进数字中国、数字经济、数字社会规划和建设等,其中第一项任务就是负责协调推进数据基础制度建设。 数字化转型网www.szhzxw.cn
构建以数据产权为基础的数据要素基础制度,其基本要旨是为了统筹推进流通交易、收益分配、安全治理协同发展的数据要素市场,更好地协调和处理与数据生产力发展相适应的数字化生产关系,以激发数据生产力乘数效应的发挥。然而,构建系统完备的数据产权制度、数据要素流通和交易制度、数据要素收益分配制度和数据要素治理制度是一项长期和复杂的社会系统工程,应按照“试点先行、以点带面”的原则,在我国数字经济较发达的地区先行先试,“数据二十条”点名“支持浙江等地区和有条件的行业、企业先行先试”。在积累和总结试点经验的基础上,再逐步在全国有条件的地区推广。在此基础上,逐步构建以“数据二十条”为纲领的“1+N”制度体系,这里的“1+N”制度体系中的“1”是指中共中央、国务院《关于构建更加完善的要素市场化配置体制机制的意见》(“数据二十条”),“N”是指围绕“数据二十条”出台多个完备的配套规定,这些配套规定主要集中在建立健全独立完备的数据产权、数据流通与交易、数据收益与分配以及数据治理等基础制度,并出台相对应的技术标准,将系统完备的“1+N”数据要素基础制度体系上升为国家法律,最终形成2.0的“1+N”数据要素法律制度,即数权法以及与其相配套的数据法律制度体系。

翻译:
Wang Chunhui: The Basic Gist of Data Element System and Compliance Enlightenment
Abstract:
The basic purpose of building a data element basic system based on data property rights is to coordinate and promote the data element market with the coordinated development of circulation transactions, income distribution, and security governance, and to better coordinate and deal with the digital production relations that are compatible with the development of data productivity. The data circulation and transaction system should reflect efficiency and compliance, the data element income distribution system should reflect efficiency and fairness, and the data element governance system should pay equal attention to security and development, and build a multi-party collaborative governance model of government, enterprises and society.
Key words: data flow; Data transaction; Data income distribution; Data governance
Data compliance and regulatory rules system for the whole process
Data is an important strategic resource for the country, and any organization or individual carrying out data processing activities must comply with laws and regulations. At present, the laws and regulations involved in the field of data supervision mainly include the Network Security Law, the Data Security Law, the Personal Information Protection Law, the Regulations on the security protection of Critical Information Infrastructure, the Regulations on the management of Network Data security, and the local data regulations formulated and promulgated by the provincial, autonomous region and municipal People’s congresses and their standing committees. 数字化转型网www.szhzxw.cn
The Cyber Security Law, officially implemented on June 1, 2017, was introduced during a severe period of international cyber security, providing a solid legal guarantee for China to effectively respond to network and data security threats and risks, and comprehensively guarantee network and data security. The Cyber Security Law is China’s first comprehensive and basic legislation in the field of network and data that covers both cyber security and data security and personal information protection. In terms of data protection, the Cybersecurity Law focuses on measures such as data classification, backup and encryption of important data, the domestic storage and exit security assessment system of important data, the maintenance of the integrity, confidentiality and availability of network data, and the definition of network data.
Article 27 of the Data Security Law
Article 27 of the Data Security Law, which came into effect on September 1, 2021, stipulates that data processors shall carry out data processing activities in accordance with the provisions of laws and regulations, and in accordance with laws and regulations, establish and improve the data security management system of the whole process, organize data security education and training, and take corresponding technical measures and other necessary measures to ensure data security. The use of the Internet and other information networks to carry out data processing activities shall fulfill the above data security protection obligations on the basis of the network security level protection system. If it is the processor of important data, it should clarify the data security responsible person and management body, and implement the data security protection responsibility.
The Data Security Law establishes a full-process security legal system of “establishing and improving the whole-process data security management system”. As required by Article 6 of the Regulations on the Security Protection of Critical Information Infrastructure, which is implemented on the same day as the Data Security Law, operators shall comply with the provisions of this Regulation and relevant laws, administrative regulations and mandatory requirements of national standards. On the basis of the level of cybersecurity protection, it adopts technical protection measures and other necessary measures to respond to cybersecurity incidents, prevent cyber attacks and illegal and criminal activities, ensure the safe and stable operation of critical information infrastructure, and maintain the integrity, confidentiality and availability of data. 数字化转型网www.szhzxw.cn
The Personal Information Protection Law clearly stipulates that the processing of personal information should follow the principles of legality, legitimacy, necessity and good faith
The Personal Information Protection Law clearly stipulates that the processing of personal information should follow the principles of legality, legitimacy, necessity and good faith, and puts forward two “minimum principles” in Article 6 of the General Provisions, that is, to adopt the way that has the least impact on the rights and interests of individuals, and is limited to the minimum scope of achieving the purpose of processing.
The two “minimum principles” of the Personal Information Protection Act are the core principles that should be followed in the processing of personal information, especially the “minimum scope” of the processing purpose, which is the key point to prohibit “excessive collection of personal information”, because personal information processors only strictly abide by the “minimum scope” of the processing purpose, that is, “no collection is necessary”. To ensure that it is done in a way that has the least impact on the rights of individuals.
According to the Regulations on the Management of Network Data Security, any individual or organization carrying out data processing activities shall abide by laws and administrative regulations, respect social morality and ethics, and shall not engage in the following six types of activities: first, endanger national security, honor and interests, divulge state secrets and work secrets; Second, it infringes on others’ right of reputation, privacy, copyright and other legitimate rights and interests; Third, by stealing or obtaining data in other illegal ways; 4. Illegally selling or illegally providing data to others; Producing, publishing, copying and disseminating illegal information; Other acts prohibited by laws and administrative regulations. 数字化转型网www.szhzxw.cn
The circulation and transaction of data elements must be carried out on the basis of security,
The circulation and transaction of data elements must be carried out on the basis of security, compliance and effective supervision, which requires the establishment of a unified national compliance and regulatory rules system for the whole process of data circulation and transaction, and focuses on strengthening the construction of a compliance governance system for market entities in the whole process of data circulation and transaction.
First of all, it is necessary to ensure that the sources of data circulation are legitimate. According to the provisions of the Data Security Law. When conducting data processing activities, it shall abide by laws and regulations, respect social morality and ethics, abide by business ethics and professional ethics, be honest and trustworthy, fulfill data security protection obligations, assume social responsibilities, and shall not endanger national security and public interests. Nor harm the legitimate rights and interests of individuals and organizations;
Secondly, to ensure the standard and compliance of data transactions
Secondly, to ensure the standard and compliance of data transactions. The standard and compliance of data transaction targets are the main index of data acquisition channels for supplier transactions that are legal, the rights are clear and undisputed, and data trading institutions can be provided with the commitment of owning complete rights and interests related to transaction data collection channels, personal information protection policies, user authorization and other related materials. And to ensure the authenticity of the transaction data, to be able to provide data trading institutions with the authenticity of the transaction data commitment and related materials. A data trading institution or a legitimate data processing institution entrusted by it shall conduct a compliance review on the legality, authenticity and source of the transaction data provided by the data provider;
Third, ensure that sensitive personal information is fully protected. According to the provisions of the Personal Information Protection Law, sensitive personal information, once leaked or illegally used, may easily lead to the violation of the human dignity of natural persons or the safety of personal life and property, mainly including biometric information, religious beliefs, specific identities, medical and health care, financial accounts, whereabouts and other information. And personal information of minors under the age of 14 数字化转型网www.szhzxw.cn
Overall construction of standard and efficient
Data trading venues The construction of data trading venues should reflect the fairness and compliance of the trading system and the orderly and efficient operation mechanism. “Data Article 20” proposes: “improve and standardize the rules of data circulation. And build a trading system that promotes the use and circulation, and combines both on and off the market.” Floor trading refers to the trading in the data exchange according to certain rules; Over-the-counter trading. That is, outside of the data exchange, the two parties are legally their own trading behavior. China’s two representative local data comprehensive legislation, the Shenzhen Special Economic Zone Data Regulation and the Shanghai Data Regulation. Both stipulate that market entities can conduct data transactions through legally established data trading (exchange) platforms. Or the transaction parties can conduct their own transactions according to law.
At present, the over-the-counter trading of data is relatively active, the on-market data trading is relatively cold, and the illegal black market data trading has formed a considerable scale, mainly involving personal information, especially personal information related to sensitive personal information, which seriously infringes on the personal information of citizens. From 2019 to October 2022, procuratorial organs nationwide approved the arrest of more than 13,000 people suspected of violating citizens’ personal information, and prosecuted more than 28,000 people. Judging from the five typical cases of crimes against citizens’ personal information released by the Supreme People’s Procuratorate in 2022, they mainly involve violations of sensitive personal information, including citizens’ credit information, biometric information, whereabouts and track information, and health and physiological information.
At the level of personal data transaction, some scholars believe that “the primary market of personal data transaction should follow the principle of informed consent
At the level of personal data transaction, some scholars believe that “the primary market of personal data transaction should follow the principle of informed consent, and the secondary market should follow the principle of legality and compatibility”, and propose corresponding amendments to Article 14, paragraph 2, Article 22 and Article 23 of China’s Personal Information Protection Law. The report to the Party’s 20th National Congress stressed the need to “strengthen the protection of personal information.”
The author believes that whether the data is traded on the floor or off the market. It should be strictly prohibited to involve the transaction of personal information that is not authorized by the individual, especially the transaction of sensitive personal information. But the personal information is anonymized except. In view of the fact that data asset trading is in the incubation period, over-the-counter data trading should be strictly regulated according to law, gradually transition from field diplomacy to field trading, transactions should be conducted in lawfully established data trading institutions, and black market data trading should be severely cracked down on to create a safe, credible and orderly data trading market environment.
According to the provisions of Article 34 of the Data Security Law,
According to the provisions of Article 34 of the Data Security Law, where laws and administrative regulations stipulate that the provision of data processing related services should obtain administrative permission, the service provider shall obtain permission according to law. In view of the particularity of data trading objects and behaviors. The access of data trading institutions shall be established in accordance with the provisions of Article 12 of the Administrative Licensing Law. It is understood that nearly 40 data exchanges have been built in China. And most of the data exchanges have repeated construction, data fragmentation and disorderly competition in the same region.
To this end, the “data 20” emphasizes that it is necessary to strengthen the design of the data trading venue system. Overall optimize the planning and layout of data trading venues, strictly control the number of trading venues. And propose the overall planning and layout of data exchanges by the newly formed National Data Bureau. 数字化转型网www.szhzxw.cn
Cultivate data element circulation and transaction service ecology
To realize the safe and efficient circulation and transaction of data elements. It is necessary to build a data circulation and transaction supply chain service ecosystem. The data supply chain transaction ecosystem service system includes data providers, buyers, platforms, regulators and third-party intermediary service providers. The most important thing here is to build a tripartite intermediary service ecosystem for data element circulation and trading. The state should cultivate a large number of professional, compliant and large-scale third-party data element professional service institutions. Including data integration, data broker, data compliance certification, data security audit, data notarization, data insurance, data custody, data asset evaluation, data dispute arbitration, data transaction risk assessment, data element personnel training. In order to greatly improve the data circulation and transaction process service capabilities and systems.
In May 2022, the Council of the European Union approved the Data Governance Act (DGA). DGA emphasizes the innovation of rules, encourages the sharing of data and improves the efficiency of data utilization. So that the circulation and utilization of data resources serve higher public policy objectives:. First, establish a re-use mechanism for data held by the public sector. Second, establish a framework to facilitate the development of data intermediaries. Thirdly, it makes standardized guidance for data altruism behavior. In promoting the use of data, DGA especially emphasizes the role of data intermediaries. Establishing data intermediary service models such as data stores, data brokers, data trusts and other data circulation and transactions. In fact, to achieve secure, reliable and efficient data circulation and transactions. The functions and roles of data brokers and data security compliance certification intermediary services are very important. 数字化转型网www.szhzxw.cn
The service content of a Data Broker is completely different from that of a data broker in the era of “digital intelligence”.
According to the definition of the Federal Trade Commission (FTC), a data broker collects consumers’ personal information through various channels. After sorting, analyzing and sharing the collected original information and derived information, sell, license, trade or provide the information to enterprises that have no direct relationship with consumers for product marketing, verifying personal identity or detecting fraud; In the era of “digital intelligence”, data brokers are not only the matching service function of collecting consumers’ personal information and data transactions through various channels. The main functions of modern data brokers’ services include a large number of value-added data services. Including data collection, aggregation, processing and processing, while providing algorithms, data storage and computing power. To provide the technical environment for circulation security. As well as to provide related consulting and agency services around data trading and circulation.
Data compliance certification is a compliance certification intermediary service to ensure the safe and efficient circulation and transaction of data elements, mainly for data security compliance certification.
According to the Implementation Rules for Data Security Management Certification. The certification mode of data security management certification includes:. Technical verification + on-site audit + post-certification supervision. In which technical verification requires a third-party technical verification body to implement data security technical verification in accordance with the certification scheme. And issue a technical verification report to the certification body and the certification client.
Technical verification institutions shall implement data security technical verification in accordance with the certification scheme, focus on monitoring the security risks of data circulation and trading activities, and when data security defects, vulnerabilities and other risks are found, they shall be obliged to take encryption, desensitization, backup, access control, audit and other technologies or other necessary measures. Strengthen data security protection in data circulation and transactions, and protect data from leakage, theft, tampering, damage, and improper use. For the protection of important data and sensitive personal information. Risk assessment shall be carried out on a regular basis for its data processing activities in accordance with regulations. And the risk assessment report shall be submitted to the relevant competent authorities.
The risk assessment report shall include the type and quantity of important data processed. The situation of data processing activities carried out, the data security risks faced and their countermeasures. At the same time, it is necessary to establish a data security management responsibility and evaluation system, develop data security protection plans, carry out security risk assessment, and organize data security compliance education and training. The certification body shall, within the validity period of the certification, continuously supervise the network operator who has obtained the certification, and reasonably determine the frequency of supervision to ensure the security and compliance of data circulation and transactions. 数字化转型网www.szhzxw.cn
Identification and evaluation of data assets
The price determination of data elements is itself a difficult problem in the development process of digital economy. If free pricing is allowed, then the data owner or controller can set a license price so high that data as a core element becomes meaningless. Therefore, in addition to bargaining transactions between data supply and demand parties. The price of data elements generally needs to be identified by establishing a data asset evaluation mechanism and formulating data value evaluation criteria.
China’s “Assets Appraisal Law” gives the definition of “assets appraisal” as
China’s “Assets Appraisal Law” gives the definition of “assets appraisal” as:. “appraisal institutions and their appraisal professionals assess and estimate the real estate, movable property, intangible assets, enterprise value, asset losses or other economic rights and interests according to the trust, and issue an appraisal report. The definition of “assets” in the Decision of the Ministry of Finance on amending the “Accounting Standards for Business Enterprises – Basic Standards” is that assets refer to the resources formed by the past transactions or events of the enterprise, owned or controlled by the enterprise, and expected to bring economic benefits to the enterprise. 数字化转型网www.szhzxw.cn
First, the past transactions or events of the enterprise include purchases, production, construction or other transactions or events. Transactions or events that are expected to occur in the future do not form assets. Secondly, owned or controlled by the enterprise means that the enterprise enjoys the ownership of a resource. Or although it does not enjoy the ownership of a resource. The resource can be controlled by the enterprise. Third, it is expected to bring economic benefits to the enterprise. Which refers to the potential of directly or indirectly causing cash and cash equivalents to flow into the enterprise. It can be seen that the formation of assets has three characteristics. One is the transaction or event that has occurred or formed. The second is owned or controlled by the enterprise. Third, it is expected to bring economic benefits to enterprises.
In 2022, the State Intellectual Property Office decided to carry out pilot programs for data intellectual property protection in Zhejiang, Shanghai, Shenzhen and other places
In 2022, the State Intellectual Property Office decided to carry out pilot programs for data intellectual property protection in Zhejiang, Shanghai, Shenzhen and other places. And strive to obtain replicable and scalable experience practices in legislation, registration and other aspects. So as to provide a practical basis for subsequent system design. During the “Two sessions” in 2023, He Zhimin, deputy director of the State Intellectual Property Office, proposed to learn from the intellectual property legal system with intangible property as the object, and establish a data intellectual property system as soon as possible. According to the “Assets Evaluation Criteria – Intangible Assets”, the identification of “intangible assets”, that is, the resources owned or controlled by a specific entity, do not have physical form, can continue to play a role and can bring economic benefits. 数字化转型网www.szhzxw.cn
International Accounting Standard 38 (IAS38) defines “intangible assets” as non-physical, identifiable non-monetary assets held for the production or supply of goods or services, leased to other entities, or for management purposes. The definition of intangible assets in China’s Accounting Standards for Business Enterprises No. 6 – Intangible assets is:. Identifiable non-monetary assets without physical form owned or controlled by enterprises. From the definition of “intangible assets” in international accounting standards and China’s accounting standards for business enterprises, . It can be seen that the basic feature of intangible assets is “recognizability”. However, data assets do not fully conform to the definition of “intangible assets” in accounting standards. And are different from traditional real estate, movable property. And identifiable non-monetary assets similar to intellectual property without physical form.
Data assets are mainly data resources that can be measured and bring direct or indirect economic benefits.
Data assets usually include three basic attributes, namely general attributes, business attributes and management attributes. First, general attributes mainly include data sources, data types, data structures, time periods, update cycles, metadata and storage forms. The second is business attributes, including business description, business model, business rules and correlation. The third is management attributes, including data classification and classification, security information, data traceability, responsibilities and permissions and application scenarios. Therefore, the evaluation of digital assets should be based on the basic attributes of digital assets, focusing on the evaluation of data value. Including the quality elements of data generation, cost elements, application value, etc. From the overall consideration of digital assets, the main weight is the quality elements and application value of data assets.
First of all, data quality elements mainly include: security, authenticity, accuracy, consistency, integrity, normalization, timeliness and compliance.
Among the above data quality factors, the most important are four elements. First, security, that is, data does not involve national security, corporate trade secrets and personal privacy information. The second is authenticity, that is. The data can accurately represent the authenticity of the things it describes in the information system. Ensuring the authenticity of the data is the first task of data asset evaluation. The third is normative, that is, data assets conform to data standards. Which cannot be simply understood as unified technical requirements in the field of data elements. But a series of normative constraints to evaluate the consistency and accuracy of data value in the process of internal and external use and exchange. The fourth is compliance, that is, data ownership, data authority, data classification, data security, infringement relief. As well as the licensed use of data, pledge, transfer, arbitration, etc.
Secondly, the application value of data assets mainly includes the scope of use, application scenario, business model, supply and demand relationship, data correlation and application risk.
The scope of use should focus on the industry, field and region involved in the data asset. Application scenarios should pay attention to the use mode, openness and frequency of data assets. The business model should focus on the model of data products and services, enabling model and financial model. The supply and demand relationship should pay attention to the scarcity, market size and value density of data assets. The data correlation should focus on the user correlation, inter-number correlation and business correlation of data assets. Application risks should focus on management risks, circulation risks, data security risks, sensitivity risks and regulatory risks of data assets. When evaluating the value of data assets, the application elements of data assets should be analyzed.
Establish a safe and compliant cross-border data circulation mechanism
The flow of data is not only limited to the country, the flow of data is global. Cross-border international trade transactions, whether import trade or export trade, need to be accompanied by cross-border data transmission. At present, the cross-border flow of data is mainly due to the need to provide data overseas for business and production. And rarely regards data itself as a commodity cross-border transaction. However. The transmission of data has moved from the original “how to transmit” into the era of “how to credibly and safely transmit”, and the construction of a safe and orderly cross-border two-way flow mechanism of data has an extremely important role for cross-border trade transactions.
The security of data exit is not only related to the development, utilization and security of data itself as an important factor of production, but also closely related to national sovereignty, national security, personal information rights and interests, and social public interests.
To this end, the “Data Article 20” requires that activities such as data processing, cross-border data transmission. And foreign mergers and acquisitions that affect or may affect national security be reviewed in accordance with laws and regulations. The data security review system is an important national security review system established by the Data Security Law. According to the provisions of Article 10 of the newly revised Network Security Review Measures in February 2022. The network security review focuses on evaluating the following national security risk factors of relevant objects or situations:
(1) The risk of illegal control, interference or destruction of critical information infrastructure caused by the use of products and services; 数字化转型网www.szhzxw.cn
(2) the disruption of the supply of products and services to the business continuity of critical information infrastructure;
(3) the safety, openness, transparency, diversity of sources of products and services, the reliability of supply channels and the risk of supply disruption due to political, diplomatic, trade and other factors;
(4) Compliance by product and service providers with Chinese laws, administrative regulations and departmental rules;
(5) The risk of core data, important data or a large amount of personal information being stolen, leaked, damaged, and illegally used or illegally left the country;
(6) There is a risk of critical information infrastructure, core data, important data or a large amount of personal information being influenced, controlled or maliciously used by foreign governments. As well as network information security risks; 数字化转型网www.szhzxw.cn
(7) Other factors that may endanger the security of critical information infrastructure, network security and data security.
Article 10 (5) (6) of the “Network Security Review Measures” is mainly aimed at the risk of core data,
Article 10 (5) (6) of the “Network Security Review Measures” is mainly aimed at the risk of core data. Important data or a large amount of personal information being stolen, leaked, damaged, and illegally used, and illegal exit. As well as the risk of critical information infrastructure, core data, important data or a large amount of personal information being influenced, controlled. And maliciously used by foreign governments. At present, China’s data legislation divides data into general data, important data, and core data. And this data classification method is mainly based on the impact and importance of data on national security, public interests. Or the legitimate rights and interests of individuals and organizations.
The “Data Article 20” requires that China actively participate in the formulation of international rules for cross-border data flows. And explore joining regional institutional arrangements for cross-border international data flows. On January 1, 2022, the Regional Comprehensive Economic Partnership (RCEP) entered into force for China. Which has made specific provisions on cross-border data flows after eight years of negotiations. 数字化转型网www.szhzxw.cn
Article 15 of the RCEP requires that “no Contracting Party shall prevent the cross-border electronic transfer of data by covered persons for the purpose of conducting business”. The RCEP also stressed that “any measure that a Party considers necessary to protect its essential security interests shall not be contested by other Parties.” It can be seen that RCEP regards the free flow of data across borders as a fundamental principle. But at the same time, RCEP respects that a sovereign country implements any security protection measures for the cross-border flow of data in the interests of national security, which includes national data security review.
In fact, the “Data Article 20” takes “cross-border data flow” as a basic principle, and only implements national security reviews on activities such as data processing, cross-border data transfer and foreign mergers and acquisitions that affect or may affect national security.
The “Data Article 20” emphasizes adhering to open development, promoting cross-border two-way and orderly flow of data, encouraging domestic and foreign enterprises and organizations to carry out cross-border data flow business cooperation in accordance with laws and regulations, supporting foreign investment to enter open fields in accordance with laws and regulations. And promoting the formation of an international market with fair competition. 数字化转型网www.szhzxw.cn
At present, data cross-border schemes have been developed in the Beijing Digital Trade Pilot Zone, Shanghai Free Trade Pilot Zone, Zhejiang Free Trade Pilot Zone and Hainan Free Trade Port. It is suggested to pilot the construction of offshore data centers in the above “free trade zones” to explore safe and standardized cross-border data flow methods, focusing on typical application scenarios such as cross-border e-commerce, cross-border payment, supply chain management, and service outsourcing. The offshore data center in the pilot free trade zone shall implement a special reciprocal policy and institutional arrangement in accordance with international rules or practices. Such as the use of the international Internet channel. So that the international data transmission in the free trade zone is more free and convenient than outside the free trade zone. And even can not implement or not fully implement the laws and regulations on data cross-border in China.
Initial distribution of data elements and government regulation function
The Decision of the Central Committee of the Communist Party of China on Several Major Issues Concerning Upholding and Improving the System of Socialism with Chinese Characteristics and Promoting the Modernization of China’s System and Capacity for Governance (hereinafter referred to as the “Decision”), adopted at the Fourth Plenary Session of the 19th CPC Central Committee, We will improve the mechanism by which the market evaluates the contribution of labor, capital, land, knowledge, technology, management, data and other factors of production, and determines their remuneration according to their contribution.
The data elements established by the “Decision” adopt the “mechanism of market evaluation of contributions and determination of remuneration according to contributions”, which points out the direction for the construction of a data element income distribution system that reflects efficiency and promotes fairness. In this regard, the “data 20” has been emphasized again. And it is also proposed to better play the guiding and regulating role of the government in the income distribution of data elements. In March 2023, the “Overall Layout Plan for the Construction of Digital China” issued by the CPC Central Committee and The State Council further pointed out that it is necessary to release the value potential of commercial data, accelerate the establishment of data property rights system, carry out data asset pricing research. And establish a mechanism for data elements to participate in the distribution according to value contribution. 数字化转型网www.szhzxw.cn
(1) Initial distribution of guiding data elements
The data itself cannot directly participate in production and distribution. But must be transformed into productive data elements through the input of each participant in the data elements. As a production factor, data should have three functions. First, data production factors can create value for the rapid economic growth. The second is the integration of data production factors with other production factors. Which has the effect of magnification and multiplication. Third, data production factors can participate in income distribution. The “Data Article 20” proposes to promote the benefit of data elements to the creators of data value and use value. Ensure that the investment in the development and mining of data value has a corresponding return. And strengthen the incentive orientation based on data value creation and value realization.
At present, we should focus on and guide the initial distribution of data elements, which is the most basic, basic and direct process of creating value by knowledge labor, and optimize the structure and weight of the initial distribution according to the characteristics of data elements.
In the initial distribution stage of data elements, the principle of “who invests, who contributes and who benefits” should be emphasized to protect the input-output income of each participant of data elements, and on the basis of improving the efficiency of data utilization, the labor value creation of data processors should be reasonable and fair. It should be emphasized here that we should pay attention to and increase the proportion of labor compensation of data processors in the initial distribution. Especially optimize the knowledge value-oriented data factor income distribution policy. Respect the role of scientific research, technology and management talents of each participant in the data factor. And fully reflect the contribution of knowledge, management and technology to the data factor market.
To ensure efficient and fair data element income distribution system and mechanism. It is necessary to give better play to the guiding and regulating role of government in data element income distribution. China’s data factor market is in the cultivation period, and the data factor income distribution system has not been established. So the fairness of the initial distribution of data factor income cannot be guaranteed by market mechanism alone. Therefore, only by giving full play to the government’s guiding and regulating role in the income distribution of data factors can the equity of the initial distribution of data factor income be realized. 数字化转型网www.szhzxw.cn
(2) Give play to the government’s regulatory function in the income distribution of data elements
In the process of digital industrialization and industrial digitization. In order to avoid the monopoly of data by large data enterprises. Thus forming a “data gap” between the data rich and the data poor. And avoid the inequity and risk caused by the polarization of the data rich and poor. The government should play a guiding and regulating role in the income distribution of data elements. On the basis of emphasizing the priority of efficiency. The data factor income distribution system should ensure the fairness of its distribution. Which is difficult to achieve only through the initial distribution of data factor market.
Therefore, the government must play a guiding and regulating role in the data factor income redistribution market and promote large data enterprises to actively assume social responsibilities. As far as possible, the “data gap” between the data rich and the data poor should be narrowed. And the data tax revenue should be invested in the real economy. Especially in the traditional manufacturing industry with digital transformation. And the focus should be on ensuring a fair data element income distribution system. 数字化转型网www.szhzxw.cn
The government should also advocate data public welfare, make better use of data, mine data. And share data, create greater economic spillovers for the public welfare of the whole society. And promote the equality of basic data public services. Data public welfare is not the egalitarianism of data distribution. Nor is it to weaken the market and government’s role in the allocation and supervision of data elements. But to let the value of data elements benefit more small, medium and micro enterprises and more people. Therefore, we must give full play to the public welfare purpose and role of data elements. And promote all people to share the dividend of data development.
Collaborative governance of data elements should reflect the security of the whole process
The governance of data elements must adhere to the principle of attaching equal importance to security and development, encouraging and standardizing at the same time. And improve the system of data element governance rules that are secure, controllable, flexible and inclusive. First of all, security should run through the whole process of data governance. And data security is an important part of national security. Data security is closely related to national political security, economic operation, social governance, public services, national defense security, and cultural security. Secondly, it is necessary to build a multi-party collaborative and participatory governance model, innovate government governance methods, clarify the main responsibilities and obligations of all parties, improve the industry self-discipline mechanism, standardize the market development order. And form a flexible and inclusive data element governance pattern that combines effective market and government.
(1) The “data element governance” system should balance innovation and regulation
The “data element governance” system is the ballast of the four basic systems of data elements. And the “data property rights, circulation transactions. And income distribution” system is the three pillars built on the basis of data governance. Without a safe, reliable and orderly “data element governance” system, there will be no data circulation and transaction. And the data rights and interests of all participants in data elements cannot be protected. 数字化转型网www.szhzxw.cn
“Data Article 20” requires that the government give full play to its role in orderly guidance and standardized development, hold the security bottom line, clarify the regulatory red line. And create a safe and credible, inclusive and innovative, fair and open. And effectively regulated data element market environment. The development of data factor market is a process of “innovation-regulation-re-innovation”. And its underlying logic is the balance of two values: innovation and security.
First of all, to pursue inclusive innovation, it is necessary to accept flawed innovation with a tolerant attitude and build a fault-tolerant and error-correcting mechanism that is inclusive of innovation. Only in this way can the development of data factor market have a strong impetus. Secondly, ensure security and credibility, security and credibility are mutually reinforcing, credibility is not equivalent to security. But credibility is the basis of security, without credibility as a guarantee. Security will be out of the question. The development of data elements market should be based on the security of trust.
The healthy development of the data factor market must not be separated from supervision and innovation.
In view of the huge potential data value generated by non-competitive data. In order to prevent the monopoly of data by large platform enterprises and eliminate competition through technological and capital advantages. The wide use of data should be encouraged as much as possible to ensure fair competition. In recent years, some large Internet platform enterprises have abused their dominant market position and carried out unfair competition. Resulting in suspected monopoly behaviors such as “big data killing” and limited transactions. 数字化转型网www.szhzxw.cn
The Personal Information Protection Law implemented in November 2021 specifically requires platform enterprises to fulfill the role of “gatekeeper” and assume more social responsibilities, including:
to establish and improve the personal information protection compliance system in accordance with national regulations. Establish an independent body composed mainly of external members to conduct oversight. To formulate platform rules in accordance with the principles of openness, fairness and justice. Stop providing services to providers of products or services within the platform that seriously violate the law in handling personal information. Regular release of personal information protection social responsibility report and accept social supervision.
In June 2022, the 35th meeting of the Standing Committee of the 13th National People’s Congress voted to adopt the decision of the Standing Committee of the National People’s Congress on amending the Anti-Monopoly Law of the People’s Republic of China, which will come into effect on August 1, 2022. The newly revised Anti-Monopoly Law clearly puts forward the “encourage innovation” in the first legislative purpose. And stipulates that operators with a dominant market position shall not use data and algorithms. Technologies and platform rules to engage in the abuse of market dominance as specified in the preceding paragraph. In this regard, the “Data 20” also clearly requires that enterprises should strictly abide by the anti-monopoly law and other relevant legal provisions, shall not use data, algorithms and other advantages and technical means to exclude, restrict competition, the implementation of unfair competition. 数字化转型网www.szhzxw.cn
Of course, the benign development of the data factor market cannot inhibit innovation and supervision, innovation is the driving force for the development of the data factor market, and supervision is the security guarantee for the development of the data factor market, and the two are dialectically unified and interrelated.
The establishment and sound development of the data factor market should adhere to both the promotion of development and regulation. And both hands should be hard, which requires the government to play the role of orderly guidance and standardized development. So that the data factor market is standardized and developed in the guidance. It is necessary to improve the data factor market access system, fair competition review system and fair competition supervision system. Establish a comprehensive, multi-level and three-dimensional supervision system. Achieve a data factor market supervision system before and after the event, the whole chain and the whole field. And form a data factor market environment that integrates fair and open with effective supervision.
(2) Strengthen the coordinated governance of the data factor market
Data factor governance is the process of gradually realizing the value creation of data factor and building a good order of data factor market. This needs to “systematically explore the ecosystem linkage mechanism of multiple subjects participating in the process of data element value”, which is a process of “multiple subjects co-creating”. “Data Article 20” proposed that we should give full play to the collaborative governance role of multi-participation of social forces.
The author believes that the collaborative governance of multi-participation of social forces mainly focuses on three major collaborative governance subjects: government, enterprises and society, in which the role of government is supervision. The obligation of enterprises is to perform responsibilities, and the function of society is supervision. First, the key system of data element security governance should be established. And the security baseline of data element circulation and utilization should be defined. Secondly, it is necessary to build a pattern of multi-subject collaboration and co-governance. And strive to enhance the trust system of the data factor market. 数字化转型网www.szhzxw.cn
“Data Article 20” proposed that it is necessary to establish a data element market credit system
“Data Article 20” proposed that it is necessary to establish a data element market credit system, and gradually improve the identification of data trading dishonesty, trustworthy incentive, dishonesty punishment, credit repair, dissent processing and other mechanisms. In January 2022, the General Plan for the Pilot Reform of Comprehensive Market-oriented Allocation of Factors issued by The General Office of the State Council stressed that it is necessary to strengthen anti-monopoly and anti-unfair competition law enforcement, regulate trading behaviors, incorporate illegal behaviors of trading entities into credit record management. And implement accountability and punishment for serious breaches of trust.
At the same time, it is necessary to carry out big data analysis of factor market transactions, and establish and improve the risk analysis, early warning prevention and classification disposal mechanism of factor transactions. Encourage the construction and development of third-party service institutions such as data registration, data value assessment, data compliance certification. And credit evaluation of transaction entities, and build and improve the data element market service system.
“Data Article 20” specifically mentions that “accelerate the implementation of national standards for data management capability maturity and data element management norms,
“Data Article 20” specifically mentions that “accelerate the implementation of national standards for data management capability maturity and data element management norms, and promote all departments and industries to improve metadata management, data desensitization, data quality, value evaluation and other standard systems. 数字化转型网www.szhzxw.cn
” The “Data Management capability Maturity National standard” here refers to China’s first national standard in the field of data management. The full name is: “Data Management Capability Maturity Assessment Model” GB/T36073-2018 (referred to as:. The reason why the “Data Article 20” requires to accelerate the implementation of DCMM is based on the fact that DCMM is the first national standard of data management capability maturity, which defines eight core competence areas in detail: data strategy, data governance, data architecture, data application, data security, data quality, data standards and data life cycle. It is subdivided into 28 process areas and 445 competency level standards, establishing relatively advanced data management concepts and methods.
The evaluation model of DCMM divides the maturity of data management capability into five levels. One level is initial level, two level is managed level, three level is robust level. Four level is quantitative management level, and five level is optimization level. These five levels are progressive relationships, from low to high level, deeper than one level. And different levels represent the differences in the level of enterprise data management and application maturity. The management concept and evaluation model of DCMM can not only help enterprises establish and evaluate their own data management capabilities. Continuously improve the data management organization, procedures and systems. But also strengthen the data management system innovation and value creation of data elements in the process of promoting the digitalization and intelligent transformation of enterprises.
Peroration
On March 10, 2023, the first session of the 14th National People’s Congress voted to pass the decision on the institutional reform plan of The State Council. And the new National Data Bureau was passed and officially began to set up. The National Data Bureau is a national bureau administered by the National Development and Reform Commission. As can be seen from the institutional reform plan of The State Council. The newly established National Data Bureau has three main tasks:. First, it is responsible for coordinating and promoting the construction of data infrastructure system. Second, coordinate the integration, sharing, development and utilization of data resources. Third, we will coordinate the planning and construction of digital China, digital economy, and digital society. Among which the first task is to coordinate and promote the construction of data infrastructure systems.
The basic purpose of building a data element basic system based on data property rights is to coordinate and promote the data element market with the coordinated development of circulation transactions
The basic purpose of building a data element basic system based on data property rights is to coordinate and promote the data element market with the coordinated development of circulation transactions, income distribution, and security governance. And better coordinate and deal with the digital production relations that are compatible with the development of data productivity. So as to stimulate the play of the multiplier effect of data productivity. However, the construction of a complete data property rights system, data element circulation and trading system. Data element income distribution system and data element governance system is a long-term and complex social system project. Which should be first tried in areas with more developed digital economy in accordance with the principle of “pilot first, point to surface”. “Data Article 20” named “support Zhejiang and other regions and conditional industries, enterprises to try first.” 数字化转型网www.szhzxw.cn
On the basis of accumulating and summarizing the pilot experience, it will be gradually promoted in all areas of the country where conditions permit.
On this basis, gradually build a “1+N” system system with “Data 20” as the program, where “1” in the “1+N” system system refers to the CPC Central Committee and The State Council’s “Opinions on Building a more perfect Market-oriented allocation system of factors” (” Data 20 “), “N” refers to the introduction of a number of complete supporting regulations around “Data 20”. These supporting regulations mainly focus on the establishment of a sound independent and complete data property rights. Data circulation and transaction, data income and distribution and data governance and other basic systems. Dnd the introduction of corresponding technical standards. The complete system of “1+N” data elements basic system to the national law. And ultimately form a 2.0 “1+N” data elements legal system. That is, the law of number weight and its matching data law system.
本文由数字化转型网(www.szhzxw.cn)转载而成,来源于国脉数据资产;编辑/翻译:数字化转型网宁檬树。

免责声明: 本网站(https://www.szhzxw.cn/)内容主要来自原创、合作媒体供稿和第三方投稿,凡在本网站出现的信息,均仅供参考。本网站将尽力确保所提供信息的准确性及可靠性,但不保证有关资料的准确性及可靠性,读者在使用前请进一步核实,并对任何自主决定的行为负责。本网站对有关资料所引致的错误、不确或遗漏,概不负任何法律责任。
本网站刊载的所有内容(包括但不仅限文字、图片、LOGO、音频、视频、软件、程序等) 版权归原作者所有。任何单位或个人认为本网站中的内容可能涉嫌侵犯其知识产权或存在不实内容时,请及时通知本站,予以删除。