今年的早些时候,暗网空间搜索引擎暗网雷达曾监控到美的巴西分公司被黑客组织Conti勒索,黑客组织Conti公布了相关勒索资料,其中包含54GB的数据。
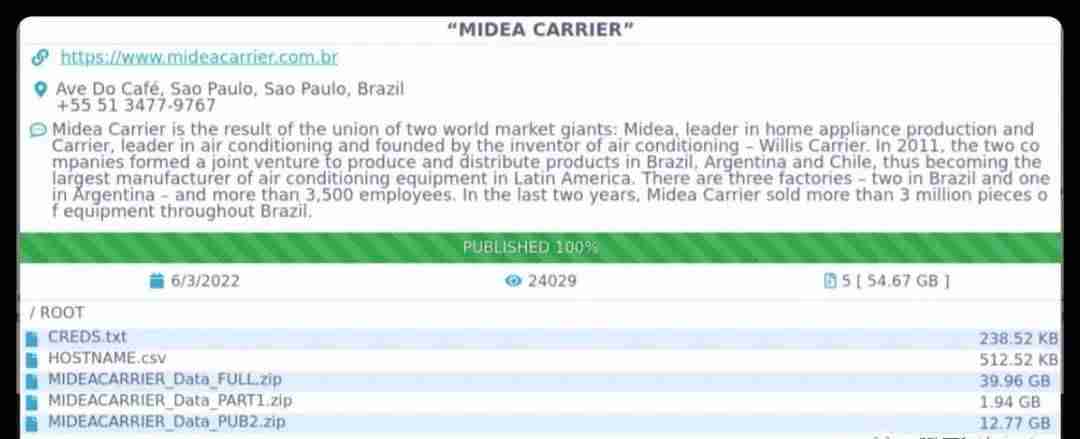
图片中的MIDEA CARRIER是美的公司和美国开利公司的合资企业,美的占股超过51%,为第一大股东,是拉美地区最大的空调厂家,也是巴西空调市场占有率第一的公司。2022年8月11日,传闻美的公司中了勒索病毒,详情可见数字化转型网(www.szhzxw.cn)文章:美的被病毒勒索1000万美金,派安保强制关机,所有内部系统无法进入,文件无法打开?美的公司回应:与事实不符
从分公司入侵其他分公司或者总部是黑客常用手段之一,由于美的官方承认了病毒,否认了勒索的存在,目前尚不清楚这两件事情是否存在关联。
一、这家名为Conti的黑客组织是何方神圣?
Conti 在 2020 年出现,Conti即是勒索病毒软件的名字,也是勒索团伙的名字,主要通过钓鱼邮件、利用其他恶意软件、漏洞利用和远程桌面协议(RDP)暴力破解进行传播,组合利用多种工具实现内网横向移动。
最常瞄准的五大行业是制造业(14%)、房地产(11.1%)、物流业(8.2%)、专业服务业(7.1%)和贸易行业(5.5%)。
自2020年以来,Conti一直在勒索软件领域占据主导地位,被其加密过数据的公司的数量仅次于Maze和Egregor团伙。根据FBI在美国的调查,仅有记录的,2021美国有1000家企业向Conti 支付了超过1.7亿美元赎金(等价虚拟货币)。
威胁情报公司 Cyberint 安全研究员萨缪尔・基恩 (Shmuel Gihon) 表示,据他估计,Conti 组织大约有 350 名成员,他们在短短两年内共赚取了约 27 亿美元 (约合 172 亿元) 的加密货币。对标国内A股头部上市安全厂商,就会发现者这是个惊人的财务数据:S公司,7000多人,21年营收60多亿,利润2亿;Q公司6500名员工,21年营收58亿,利润负5亿。不由得感叹,黑道真是比白道赚钱,Conti 作为IT江湖中的冒尖IT黑道团伙,真是世界上赚钱的黑帮之一了。
二、为啥Conti这么赚钱
(一)Conti勒索组织是双重勒索攻击的典型代表
一个原因是Conti勒索组织是双重勒索攻击的典型代表,双重勒索攻击是区别于传统的加密数据-勒索赎金的攻击方式,双重勒索会在加密目标数据之前,先将部分机密数据进行下载。
双重勒索手中有两个筹码,一是加密数据解密数据勒索,除此之外,攻击者手中还掌握了另一个勒索筹码,即在网站上泄露一小部分预先下载的数据。对于美的开利的攻击就属于双重勒索攻击,Conti将54G的数据(可能只是部分)挂在了网上作为威胁,如不支付赎金,就会公开这部分企业机密数据。
由于大多数企业会对数据进行备份,比如每隔12个小时备份一次,一旦数据被勒索软件加密只需要杀毒,并恢复备份即可,一般只损失当天部分数据。很多企业面临勒索病毒攻击时候会优先考虑损失部分数据而恢复备份的方式,但对于双重攻击勒索病毒来讲,只恢复备份是不够的的。
当企业使用备份替代等方式,拒绝支付赎金获取解密工具时,他们会再次威胁目标用户,如果不支付赎金将数据全部公开,或者在放在暗网上公开售卖,以此提高勒索成功率。
C团队勒索的都是大公司,这些大公司的销售价格数据、内部人员薪资数据、订单数据、成本数据、新产品研发资料和文档,乃至生产过程中的一些工艺、技术参数,对于大公司来讲都是核心竞争力和核心机密。这些数据一旦被公开,会引起同行抄袭、客户不满。
很多大公司还有一些见不得人的数据,比如违反法律的数据:财务税务造假、环保造假、质量造假、工人超法定时间工作,非法雇佣等等,当这些数据被公开,会引发一些社会舆论谴责乃至被政府调查、罚款和破产的风险。
因而,有相当一部分受害者是因为害怕企业机构的机密数据(以及见不得人的数据)被曝光而支付了赎金。综上所述,大部分被Conti勒索或中了双重勒索攻击的公司都不敢声张。
这些资料可能吸引不怀好意者比如竞争对手出钱购买,这会加大勒索方要价的筹码。
(二)Conti非常有职业道德
另一个使Conti暴富的原因是Conti非常有职业道德,区别于一些付了钱也照样不归还数据,甚至完全联系不到的勒索病毒诈骗分子,当目标公司支付赎金时,Conti会全力保护受害者的数据资产和数据恢复。
如果目标公司对于数据恢复有技术疑问,Conti 甚至还雇佣了一些技术支持人员来协助已支付赎金的受害者进行数据恢复。Conti 还雇佣了一些商务谈判专家,根据目标的付费意愿和经济实力的实际情况来协商赎金。这种方式也被业内专家调侃为RAAS模式:勒索软件即服务。
这种收钱办事,讲道理讲江湖规矩的黑客,颇像传统社会讲江湖道义的黑道和黑帮。有激进人士对于Conti 这种瞄准大公司,通过绑架数据资产抢大户的行为拍手叫好,认为他们是信息化数字化时代的侠客,劫富济贫。
2021年2月,美国警方抓获了一位名叫黑客界鼎鼎有名的女黑客阿拉·维特(Alla Witte),Conti的高层主动为她找了当地最好的律师,并决定支付所有相关的辩护费用。
三、Conti 的运营团队是一个经典的科技公司层次结构
Conti 组织分工明确,顶层是大老板,下面分别是HR管理层 ,blog记录招聘,培训组、区块链组、 A组红队、B组反恐特警组还有红队和保卫团队的开发组、渗透测试组、逆向工程师、和质检 ,还有开源情报组等等。
种种迹象表明,Conti 核心成员主要在俄语地区,其主要使用俄语沟通,还使用过中国软件工具,或许有华人成员。
成员Stern :大boss,负责集团运营和与附属公司合作,并直接和间接地管理许多人员和项目。成员Bentley:技术负责人,负责测试和防御规避。成员Mango:主要协调解决负责攻击人员和开发人员之间的问题。成员Buza:负责开发和产品,在开发团队中策划加载器和bot的开发。成员Target:负责管理黑客团队,他还负责管理所有线下办公场所。成员Veron:管理Emotet木马软件活动的所有资源,包括基础设施。
Conti 招聘了大量的开发人员,如全栈开发人员、加密开发人员、C++ 开发人员和 php 开发人员。这些为黑客组织打工的码农们,并不知道自己是在一家黑客组织里,干的活和西二旗的IT公司差不多。
他们做五休二,月薪在1000到2000美元之间。由于Conti内部分工明确,每个环节的工作都相对固定,致使许多黑客的工作其实就是机械的重复性劳动,非常无聊。比如有的底层黑客每4小时就要进行一次软件测试,有的黑客每天的工作就是发邮件。因而导致离职率非常高,Conti的HR每月都会花数千美元去各大求职网站的招人,物色优秀的“后备黑客人才”,这里面除了码农还有客服、商务BD、市场新媒体、催收等等。
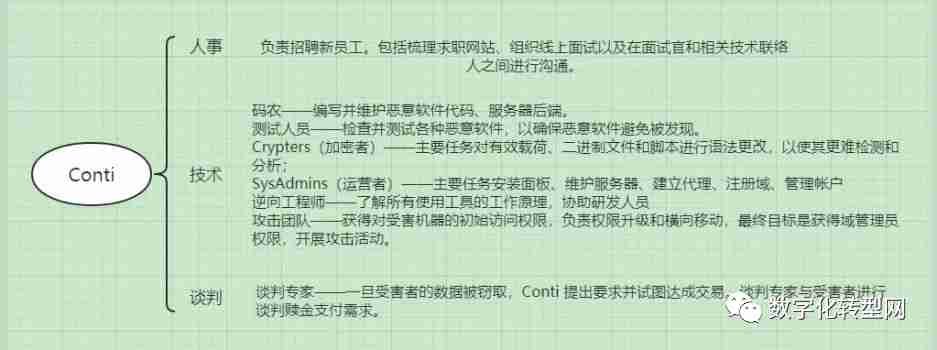
Conti 的运营团队是一个经典的科技公司层次结构,环环相扣,各尽其责,可以看出其骨干成员应该来自一些大型信息安全公司。结合其俄罗斯的背景,让人不由得联想到其创始团队是不是来自卡巴斯基?
和一般鬼鬼祟祟的黑客不同,Conti团伙在线下拥有多个实体办公室,这些由Stern的合伙人运营,线下办公主要供测试人员、进攻团队和谈判人员使用。其中还有几个专门为与受害者代表进行直接对话的办公室,用来接待受害企业代表和进行商务谈判。
Conti还制定了发展计划,进行黑客相关的产品孵化。比如其中之一是暗网社交网络,(又名:“VK for darknet”或“Carbon Black for hackers”),计划作为商业项目进行开发,计划打造一个黑客人士专属的LinkedIn或Facebook。此外还研发加密系统,计划在组织内部建立一套私有密钥交换系统。
Conti明显遵守着俄语网络犯罪圈的潜规则,不攻击俄罗斯公司,重点攻击西方国家,其80%以上的攻击对象都在欧美:美国(58.4%),加拿大(7%)、英国(6.6%)、德国(5.8%)、法国(3.9%)和意大利(3.1%)。
Conti曾经在美国的后院放火,声称要通过网络攻击推翻哥斯达黎加政府,攻击了27个政府部门,加密了所有数据和档案,致使大部分公共机构迅速陷入瘫痪,让民众无法正常缴纳电费,政府雇员无法领工资,海关仅在一个周三就损失超过2亿美元。他们还呼吁哥斯达黎加老百姓上街游行,给政府施压缴纳赎金。
美国国务院通过情报系统,找到了Conti核心成员Target的外貌,向社会各界悬赏捉拿这几位核心成员,为提供以上6名的成员信息的人提供了高达1000万美元的悬赏奖励。这种劫掠西方发达富裕国家企业的行径,暗中受到不少对美国等发达国家不满的人员的支持,甚至吸引对美国持敌对态度的黑客主动报名加入。
受乌俄战争内讧和美国悬赏的影响,肆虐2年后,恶名昭彰的勒索软件Conti于今年5月悄悄关闭了官网和收赎金的服务器,宣告关门大吉。只是这次关闭的是Conti勒索软件的「品牌」,并非Conti背后的黑客团队,也就是作为勒索组织的Conti并非退出江湖,还是会以新的品牌继续活动。当然也不存在退出江湖,只要有IT江湖就有黑客来劫掠。
早在2月内讧之时,Conti就悄悄搞了KaraKurt、BlackByte、BlackBasta等几个新品牌对外进行活动。黑客组织犹如野火烧不尽,春风吹又生。只要有企业进行数字化,进行数字化转型,就有属于数字化的江湖,有江湖的地方就有黑道、黑帮和黑客,Conti只是众多IT黑道团伙中的冰山一角。
企业在数字化转型时候需每年做好IT安全预算,用来进行安全系统建设,提高防范意识,降低被黑客入侵和勒索的风险。
翻译:
Earlier this year, Dark Web radar, a search engine for dark web space, caught a US firm in Brazil being blackmailed by the hacker group Conti. Conti released the ransom files containing 54 gigabytes of data.
Conti, a hacking group, released the ransom material, which contained 54 gigabytes of data
MIDEA CARRIER in the picture is a joint venture between Midea and Carrier. Midea holds more than 51% of the shares, making it the largest shareholder. Midea is the largest air conditioner manufacturer in Latin America and the company with the largest market share in Brazil. On August 11, 2022, Midea was rumored to be in the ransomware virus, details can be seen on www.szhzxw.cn article: Midea was extorted 10 million dollars by the virus, sent security forces to shut down, all internal systems cannot be entered, files cannot be opened? Midea’s response: inconsistent with the facts
Hacking into other branches or headquarters is one of the most common methods used by hackers. As Midea officials acknowledged the virus and denied the existence of the extortion, it was not clear if the two incidents were related.
1、Who is the hacker group called Conti?
Conti emerged in 2020. Conti is the name of ransomware, and the name of a ransomware group that spreads through phishing emails, other malware, vulnerability exploitation, and Remote Desktop Protocol (RDP) brute force cracking, using a combination of tools to move the Intranet sideways.
The five most commonly targeted industries were manufacturing (14 per cent), real estate (11.1 per cent), logistics (8.2 per cent), professional services (7.1 per cent) and trade (5.5 per cent).
Conti has dominated ransomware since 2020, trailing only Maze and the Egregor gang in the number of companies whose data it has encrypted. According to an FBI investigation in the US, only 1,000 companies in the US recorded paying more than $170m (virtual currency equivalent) to Conti in 2021.
Shmuel Gihon, a security researcher at threat intelligence firm Cyberint, said he estimated that the Conti group had about 350 members who had collectively made about $2.7 billion in cryptocurrencies in just two years. To mark the top listed domestic A-share security manufacturers, you will find this is an amazing financial data: S company, more than 7,000 people, 21 years of revenue of more than 6 billion, profit of 200 million; Q Company has 6,500 employees, 21 years revenue of 5.8 billion, profit of negative 500 million. Can not help but sigh, Mafia is more than white money, Conti as IT river’s lake in IT Mafia gang, is one of the world to make money.
2、why Conti makes so much money
(I) Conti extortion organization is a typical representative of double extortion attacks
One reason is that Conti Ransomware is a typical example of a dual ransomware attack, which is different from the traditional encrypted data for ransom, in which some classified data is downloaded before being encrypted.
Double blackmail has two chips, one is encryption and decryption of data extortion, in addition, the attacker also holds another extortion chip, that is, a small portion of the pre-downloaded data leaked on the website. The Midea Carrier attack was a double blackmail attack, in which Conti posted 54 gigabytes of data (possibly only part of it) online as a threat to release confidential corporate data unless a ransom was paid.
Since most enterprises back up data, such as every 12 hours, once the data is encrypted by the ransomware, they only need to remove the virus and restore the backup, which generally only loses part of the data of the day. Many enterprises, faced with a ransomware attack, will prioritize restoring a backup after losing some data, but for a double-attack ransomware, restoring a backup is not enough.
When companies refuse to pay the ransom to obtain decryption tools, such as backup replacement, they will threaten the target users again, unless they pay the ransom to disclose all the data, or publicly sell it on the dark web, in order to increase the success rate of blackmail.
What Team C blackmailed were all large companies, whose sales price data, internal staff salary data, order data, cost data, new product research and development data and documents, as well as some processes and technical parameters in the production process, were all core competitiveness and core secrets for large companies. Such data, once made public, will lead to peer copying and customer dissatisfaction.
Many large companies also have some shady data, such as data that violates the law: financial and tax fraud, environmental protection fraud, quality fraud, workers working overtime, illegal employment and so on. When these data are made public, it will cause some social condemnation and even be investigated by the government, fines and bankruptcy risk.
As a result, a significant number of victims pay the ransom for fear that confidential (and shady) corporate data will be exposed. All told, most of the companies that were blackmailed by Conti or hit by a double blackmail attack were afraid to speak up.
The data could attract money from a hostile party, such as a rival, which would increase the extortion party’s leverage.
(Two) Conti has a great work ethic
Another reason Conti has become rich is that Conti has a very strong work ethic. Unlike ransomware scammers, who do not return data even after paying for it, or cannot be contacted at all, when a target company pays, Conti goes all out to protect the victim’s data assets and data recovery.
Conti has even hired some technical support staff to assist victims who have paid ransoms if the target company has technical questions about data recovery. Conti also employs business negotiators to negotiate ransoms based on the target’s willingness to pay and the reality of his financial strength. This approach has also been mocked by industry experts as the RAAS model: ransomware as a service.
This kind of hackers who take money to do things and talk about the rules of the river and lake are quite like the triads and gangsters who talk about the morality of the river and lake in the traditional society. Some activists applaud Conti for targeting big companies and grabbing big players by kidnapping data assets, saying they are the vigilantes of the information and digital age, robbing the rich to give to the poor.
When Alla Witte, one of the most famous hackers in the world, was arrested by the US police in February 2021, Conti’s top management took it upon themselves to find the best local lawyers for her and agreed to pay all related defense costs.
Third, Conti’s operations team is a classic tech company hierarchy
Conti organization clear division of labor, the top is the big boss, the following are HR management, blog record recruitment, training group, blockchain group, A group of red team, B group of anti-terrorism SWAT and red team and security team of the development group, penetration test group, reverse engineer, and quality control, as well as open source intelligence group and so on.
The indications are that Conti’s core members are mainly in Russian-speaking areas, that it mainly communicates in Russian, that it has used Chinese software tools, and that it may have Chinese members.
Member Stern: Big boss, responsible for group operations and working with affiliates, and directly and indirectly managing many people and projects. Member Bentley: Technical Lead, responsible for testing and avoidance defense. Member Mango: Mainly coordinates and solves problems between those responsible for attacks and developers. Member Buza: Responsible for development and products, planned the development of loaders and bots in the development team. Member Target: Manages the hacker team, and he also manages all offline offices. Member Veron: Manages all resources for Emotet Trojan software activities, including infrastructure.
Conti hires a large number of developers, such as full stack developers, encryption developers, C++ developers, and php developers. These code farmers who work for hacker organizations do not know that they are in a hacker organization, doing work and the West second Banner IT company.
They work five days off and earn between $1,000 and $2,000 a month. Because Conti internal division of labor is clear, each link of the work is relatively fixed, resulting in many hackers work is actually mechanical repetitive labor, very boring. For example, some low-level hackers have to run software tests every four hours, and some hackers have to send emails every day. As a result, the turnover rate was so high that Conti’s HR staff spent thousands of dollars a month on job sites looking for “backup hacker talent,” which included customer service, business BD, marketing and new media, collection, etc.
Conti’s operations team is a classic tech company hierarchy, interlocking and doing their own things, and you can see the backbone coming from some of the larger information security companies. Given its Russian background, one can’t help but wonder if the founding team is from Kaspersky.
Unlike your average sneaky hacker, the Conti gang has multiple physical offices, run by Stern’s partners, that are mostly used by testers, offensive teams and negotiators. There are also several offices dedicated to direct dialogue with victims’ representatives, which are used to receive victims’ business representatives and conduct business negotiations.
Conti also has a development plan for hacker-related product incubation. One of them, for example, is the Dark Web social network (aka “VK for darknet” or “Carbon Black for hackers”), intended to be developed as a business project, aiming to create a LinkedIn or Facebook for hackers. In addition to developing encryption systems, plans to establish a private key exchange system within the organization.
Conti clearly adhered to the unspoken rules of Russian-language cybercrime circles, avoiding Russian companies and focusing on Western countries, with more than 80 percent of its targets in the US and Europe: the US (58.4 percent), Canada (7 percent), the UK (6.6 percent), Germany (5.8 percent), France (3.9 percent) and Italy (3.1 percent).
Conti once set fire to the backyard of the United States and claimed to overthrow the Costa Rican government through cyberattacks, attacking 27 government departments, encrypting all data and archives, quickly bringing most public institutions to a standstill, leaving people unable to pay their electricity bills, government employees unable to collect their salaries, and customs costing more than $200 million on Wednesday alone. They also called on ordinary Costa Ricans to take to the streets to pressure the government to pay the ransom.
The U.S. State Department, through its intelligence system, found the appearance of Target, a key member of Conti, and offered a reward of up to $10 million to anyone who could provide information on the six members. Such acts of looting western developed and rich countries’ enterprises are secretly supported by many people who are dissatisfied with the United States and other developed countries, and even attract hackers who are hostile to the United States.
After two years of fighting between Russia and Ukraine and a bounty from the United States, the notorious ransomware Conti quietly shut down its website and ransom-collecting server in May. Only this time it was the Conti ransomware “brand” that was shut down, not the hacking team behind Conti, meaning that Conti as a ransomware organization is not quitting, or will continue to operate under a new brand. Of course, there is no exit lake, as long as there is IT lake there will be hackers to plunder.
As early as February, Conti quietly promoted several new brands including KaraKurt, BlackByte, and BlackBasta. Hacker groups are like wildfire, spring wind blowing. As long as there are enterprises to digitize, digital transformation, there will be digital rivers and lakes, where there are gangs, gangs and hackers, Conti is just the tip of the iceberg of many IT gangs.
During the digital transformation, enterprises need to make an annual IT security budget to build security systems, improve prevention awareness, and reduce the risk of being hacked and extorted.
本文系数字化转型网(www.szhzxw.cn)原创而得,本文作者:数字化转型网木铎;编辑:数字化转型网默然。

免责声明: 本网站(https://www.szhzxw.cn/)内容主要来自原创、合作媒体供稿和第三方投稿,凡在本网站出现的信息,均仅供参考。本网站将尽力确保所提供信息的准确性及可靠性,但不保证有关资料的准确性及可靠性,读者在使用前请进一步核实,并对任何自主决定的行为负责。本网站对有关资料所引致的错误、不确或遗漏,概不负任何法律责任。
本网站刊载的所有内容(包括但不仅限文字、图片、LOGO、音频、视频、软件、程序等) 版权归原作者所有。任何单位或个人认为本网站中的内容可能涉嫌侵犯其知识产权或存在不实内容时,请及时通知本站,予以删除。